#include <tls_server_impl_12.h>
Public Member Functions | |
| void | close () |
| bool | expects_downgrade () const |
| std::optional< std::string > | external_psk_identity () const override |
| std::unique_ptr< Downgrade_Information > | extract_downgrade_info () |
| size_t | from_peer (std::span< const uint8_t > data) override |
| bool | is_active () const override |
| bool | is_closed () const override |
| bool | is_closed_for_reading () const override |
| bool | is_closed_for_writing () const override |
| bool | is_downgrading () const |
| bool | is_handshake_complete () const override |
| SymmetricKey | key_material_export (std::string_view label, std::string_view context, size_t length) const override |
| virtual bool | new_session_ticket_supported () const |
| std::vector< X509_Certificate > | peer_cert_chain () const override |
| std::shared_ptr< const Public_Key > | peer_raw_public_key () const override |
| void | renegotiate (bool force_full_renegotiation=false) override |
| bool | secure_renegotiation_supported () const override |
| void | send_alert (const Alert &alert) override |
| void | send_fatal_alert (Alert::Type type) |
| virtual size_t | send_new_session_tickets (const size_t) |
| void | send_warning_alert (Alert::Type type) |
| Server_Impl_12 (const Channel_Impl::Downgrade_Information &downgrade_info) | |
| Server_Impl_12 (const std::shared_ptr< Callbacks > &callbacks, const std::shared_ptr< Session_Manager > &session_manager, const std::shared_ptr< Credentials_Manager > &creds, const std::shared_ptr< const Policy > &policy, const std::shared_ptr< RandomNumberGenerator > &rng, bool is_datagram=false, size_t reserved_io_buffer_size=TLS::Channel::IO_BUF_DEFAULT_SIZE) | |
| bool | timeout_check () override |
| void | to_peer (std::span< const uint8_t > data) override |
| void | update_traffic_keys (bool request_peer_update=false) override |
Protected Attributes | |
| std::unique_ptr< Downgrade_Information > | m_downgrade_info |
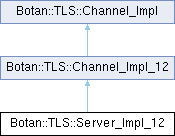
Detailed Description
SSL/TLS Server 1.2 implementation
Definition at line 24 of file tls_server_impl_12.h.
Constructor & Destructor Documentation
◆ Server_Impl_12() [1/2]
|
explicit |
Server initialization
- Parameters
-
callbacks contains a set of callback function references required by the TLS server. session_manager manages session state creds manages application/user credentials policy specifies other connection policy information rng a random number generator is_datagram set to true if this server should expect DTLS connections. Otherwise TLS connections are expected. reserved_io_buffer_size This many bytes of memory will be preallocated for the read and write buffers. Smaller values just mean reallocations and copies are more likely.
Definition at line 264 of file tls_server_impl_12.cpp.
References BOTAN_ASSERT_NONNULL, Botan::TLS::Channel_Impl_12::callbacks(), Botan::TLS::Channel_Impl_12::Channel_Impl_12(), Botan::TLS::Channel_Impl_12::policy(), Botan::TLS::Channel_Impl_12::rng(), and Botan::TLS::Channel_Impl_12::session_manager().
◆ Server_Impl_12() [2/2]
|
explicit |
Definition at line 275 of file tls_server_impl_12.cpp.
References Botan::TLS::Channel_Impl_12::callbacks(), Botan::TLS::Channel_Impl_12::Channel_Impl_12(), Botan::TLS::Channel_Impl_12::policy(), Botan::TLS::Channel_Impl_12::rng(), and Botan::TLS::Channel_Impl_12::session_manager().
Member Function Documentation
◆ activate_session()
|
protectedinherited |
Definition at line 266 of file tls_channel_impl_12.cpp.
References Botan::TLS::Channel_Impl::application_protocol(), BOTAN_ASSERT_NONNULL, callbacks(), Botan::map_remove_if(), and Botan::TLS::Callbacks::tls_session_activated().
◆ active_state()
|
inlineprotectedinherited |
Definition at line 153 of file tls_channel_impl_12.h.
◆ callbacks()
|
inlineprotectedinherited |
Definition at line 185 of file tls_channel_impl_12.h.
Referenced by activate_session(), Channel_Impl_12(), Botan::TLS::Client_Impl_12::Client_Impl_12(), Botan::TLS::Client_Impl_12::Client_Impl_12(), key_material_export(), Botan::TLS::Server_Impl_12::Server_Impl_12(), and Botan::TLS::Server_Impl_12::Server_Impl_12().
◆ change_cipher_spec_reader()
|
protectedinherited |
Definition at line 202 of file tls_channel_impl_12.cpp.
References BOTAN_ASSERT, Botan::TLS::Client, and Botan::TLS::Server.
◆ change_cipher_spec_writer()
|
protectedinherited |
Definition at line 229 of file tls_channel_impl_12.cpp.
References BOTAN_ASSERT.
◆ close()
|
inlineinherited |
Send a close notification alert
Definition at line 76 of file tls_channel_impl.h.
References send_warning_alert().
◆ create_handshake_state()
|
protectedinherited |
Definition at line 117 of file tls_channel_impl_12.cpp.
References Botan::TLS::Policy::dtls_default_mtu(), Botan::TLS::Policy::dtls_initial_timeout(), Botan::TLS::Policy::dtls_maximum_timeout(), Botan::TLS::Protocol_Version::is_datagram_protocol(), new_handshake_state(), policy(), and Botan::TLS::Protocol_Version::to_string().
Referenced by Botan::TLS::Client_Impl_12::Client_Impl_12(), Botan::TLS::Client_Impl_12::Client_Impl_12(), and renegotiate().
◆ expects_downgrade()
|
inlineinherited |
Definition at line 276 of file tls_channel_impl.h.
References m_downgrade_info.
Referenced by Botan::TLS::Client_Impl_13::Client_Impl_13(), and Botan::TLS::Channel_Impl_13::from_peer().
◆ external_psk_identity()
|
overridevirtualinherited |
Implements Botan::TLS::Channel_Impl.
Definition at line 107 of file tls_channel_impl_12.cpp.
◆ extract_downgrade_info()
|
inlineinherited |
- See also
- Downgrade_Information
Definition at line 274 of file tls_channel_impl.h.
References m_downgrade_info.
◆ from_peer()
|
overridevirtualinherited |
Inject TLS traffic received from counterparty
- Returns
- a hint as the how many more bytes we need to q the current record (this may be 0 if on a record boundary)
Implements Botan::TLS::Channel_Impl.
Definition at line 293 of file tls_channel_impl_12.cpp.
References Botan::TLS::Alert, Botan::TLS::Policy::allow_dtls_epoch0_restart(), Botan::TLS::ApplicationData, BOTAN_ASSERT, BOTAN_ASSERT_IMPLICATION, Botan::TLS::ChangeCipherSpec, Botan::TLS::ClientHello, Botan::TLS::Record_Header::epoch(), Botan::TLS::Handshake, Botan::TLS::Invalid, Botan::TLS::Protocol_Version::major_version(), Botan::TLS::MAX_PLAINTEXT_SIZE, Botan::TLS::Record_Header::needed(), policy(), Botan::TLS::read_record(), Botan::TLS::Channel_Impl::send_fatal_alert(), Botan::TLS::Record_Header::sequence(), Botan::TLS::Record_Header::type(), Botan::TLS::TLS_Exception::type(), and Botan::TLS::Record_Header::version().
◆ inspect_handshake_message()
|
protectedinherited |
◆ is_active()
|
overridevirtualinherited |
- Returns
- true iff the connection is active for sending application data
Implements Botan::TLS::Channel_Impl.
Definition at line 258 of file tls_channel_impl_12.cpp.
References is_closed(), and is_handshake_complete().
Referenced by to_peer().
◆ is_closed()
|
overridevirtualinherited |
- Returns
- true iff the connection has been definitely closed
Implements Botan::TLS::Channel_Impl.
Definition at line 262 of file tls_channel_impl_12.cpp.
Referenced by is_active(), is_closed_for_reading(), is_closed_for_writing(), and send_alert().
◆ is_closed_for_reading()
|
inlineoverridevirtualinherited |
- Returns
- true iff the connection is active for sending application data
Implements Botan::TLS::Channel_Impl.
Definition at line 95 of file tls_channel_impl_12.h.
References is_closed().
◆ is_closed_for_writing()
|
inlineoverridevirtualinherited |
- Returns
- true iff the connection has been definitely closed
Implements Botan::TLS::Channel_Impl.
Definition at line 97 of file tls_channel_impl_12.h.
References is_closed().
◆ is_downgrading()
|
inlineinherited |
Indicates whether a downgrade to TLS 1.2 or lower is in progress
- See also
- Downgrade_Information
Definition at line 269 of file tls_channel_impl.h.
References m_downgrade_info.
Referenced by Botan::TLS::Channel_Impl_13::from_peer(), Botan::TLS::Channel_Impl_13::key_material_export(), and Botan::TLS::Channel_Impl_13::update_traffic_keys().
◆ is_handshake_complete()
|
overridevirtualinherited |
- Returns
- true iff the TLS handshake completed successfully
Implements Botan::TLS::Channel_Impl.
Definition at line 254 of file tls_channel_impl_12.cpp.
Referenced by is_active().
◆ key_material_export()
|
overridevirtualinherited |
Key material export (RFC 5705)
- Parameters
-
label a disambiguating label string context a per-association context value length the length of the desired key in bytes
- Returns
- key of length bytes
Implements Botan::TLS::Channel_Impl.
Definition at line 653 of file tls_channel_impl_12.cpp.
References Botan::as_span_of_bytes(), callbacks(), Botan::concat(), Botan::store_be(), and Botan::TLS::Callbacks::tls12_protocol_specific_kdf().
◆ new_handshake_state()
|
protectedpure virtualinherited |
Referenced by create_handshake_state().
◆ new_session_ticket_supported()
|
inlinevirtualinherited |
- Returns
- true if this channel can issue TLS 1.3 style session tickets.
Reimplemented in Botan::TLS::Server_Impl_13.
Definition at line 140 of file tls_channel_impl.h.
◆ peer_cert_chain()
|
overridevirtualinherited |
- Returns
- certificate chain of the peer (may be empty)
Implements Botan::TLS::Channel_Impl.
Definition at line 100 of file tls_channel_impl_12.cpp.
◆ peer_raw_public_key()
|
inlineoverridevirtualinherited |
Note: Raw public key for authentication (RFC7250) is currently not implemented for TLS 1.2.
- Returns
- raw public key of the peer (will be nullptr)
Implements Botan::TLS::Channel_Impl.
Definition at line 110 of file tls_channel_impl_12.h.
◆ policy()
|
inlineprotectedinherited |
Definition at line 183 of file tls_channel_impl_12.h.
Referenced by Channel_Impl_12(), Botan::TLS::Client_Impl_12::Client_Impl_12(), Botan::TLS::Client_Impl_12::Client_Impl_12(), create_handshake_state(), from_peer(), renegotiate(), Botan::TLS::Server_Impl_12::Server_Impl_12(), and Botan::TLS::Server_Impl_12::Server_Impl_12().
◆ preserve_client_hello()
|
inlineprotectedinherited |
Definition at line 229 of file tls_channel_impl.h.
References BOTAN_STATE_CHECK, and m_downgrade_info.
Referenced by Botan::TLS::Client_Impl_13::Client_Impl_13().
◆ preserve_peer_transcript()
|
inlineprotectedinherited |
Definition at line 224 of file tls_channel_impl.h.
References BOTAN_STATE_CHECK, and m_downgrade_info.
Referenced by Botan::TLS::Channel_Impl_13::from_peer().
◆ renegotiate()
|
overridevirtualinherited |
Attempt to renegotiate the session
- Parameters
-
force_full_renegotiation if true, require a full renegotiation, otherwise allow session resumption
Implements Botan::TLS::Channel_Impl.
Definition at line 182 of file tls_channel_impl_12.cpp.
References Botan::TLS::Policy::allow_resumption_for_renegotiation(), create_handshake_state(), initiate_handshake(), and policy().
◆ request_downgrade()
|
inlineprotectedinherited |
Implementations use this to signal that the peer indicated a protocol version downgrade. After calling request_downgrade() no further state changes must be performed by the implementation. Particularly, no further handshake messages must be emitted. Instead, they must yield control flow back to the underlying Channel implementation to perform the protocol version downgrade.
Definition at line 250 of file tls_channel_impl.h.
References BOTAN_STATE_CHECK, and m_downgrade_info.
Referenced by request_downgrade_for_resumption().
◆ request_downgrade_for_resumption()
|
inlineprotectedinherited |
Definition at line 255 of file tls_channel_impl.h.
References BOTAN_ASSERT_NOMSG, BOTAN_STATE_CHECK, Botan::TLS::Protocol_Version::is_pre_tls_13(), m_downgrade_info, request_downgrade(), Botan::TLS::Session_with_Handle::session, and Botan::TLS::Session_Base::version().
Referenced by Botan::TLS::Client_Impl_13::Client_Impl_13().
◆ reset_active_association_state()
|
protectedinherited |
Definition at line 62 of file tls_channel_impl_12.cpp.
References BOTAN_ASSERT_NOMSG.
◆ rng()
|
inlineprotectedinherited |
Definition at line 179 of file tls_channel_impl_12.h.
Referenced by Channel_Impl_12(), Botan::TLS::Client_Impl_12::Client_Impl_12(), Botan::TLS::Client_Impl_12::Client_Impl_12(), Botan::TLS::Server_Impl_12::Server_Impl_12(), and Botan::TLS::Server_Impl_12::Server_Impl_12().
◆ secure_renegotiation_check() [1/2]
|
protectedinherited |
Definition at line 588 of file tls_channel_impl_12.cpp.
References BOTAN_ASSERT_NONNULL, Botan::CT::is_equal(), Botan::TLS::Client_Hello_12::renegotiation_info(), Botan::TLS::Client_Hello_12::secure_renegotiation(), and secure_renegotiation_data_for_client_hello().
Referenced by Botan::TLS::Client_Impl_12::Client_Impl_12().
◆ secure_renegotiation_check() [2/2]
|
protectedinherited |
Definition at line 606 of file tls_channel_impl_12.cpp.
References BOTAN_ASSERT_NONNULL, Botan::CT::is_equal(), Botan::TLS::Server_Hello_12::renegotiation_info(), Botan::TLS::Server_Hello_12::secure_renegotiation(), and secure_renegotiation_data_for_server_hello().
◆ secure_renegotiation_data_for_client_hello()
|
protectedinherited |
Definition at line 624 of file tls_channel_impl_12.cpp.
Referenced by secure_renegotiation_check().
◆ secure_renegotiation_data_for_server_hello()
|
protectedinherited |
Definition at line 631 of file tls_channel_impl_12.cpp.
References Botan::concat().
Referenced by secure_renegotiation_check().
◆ secure_renegotiation_supported()
|
overridevirtualinherited |
- Returns
- true iff the counterparty supports the secure renegotiation extensions.
Implements Botan::TLS::Channel_Impl.
Definition at line 639 of file tls_channel_impl_12.cpp.
◆ send_alert()
|
overridevirtualinherited |
Send a TLS alert message. If the alert is fatal, the internal state (keys, etc) will be reset.
- Parameters
-
alert the Alert to send
Implements Botan::TLS::Channel_Impl.
Definition at line 560 of file tls_channel_impl_12.cpp.
References Botan::TLS::Alert, is_closed(), Botan::TLS::Alert::is_fatal(), Botan::TLS::Alert::is_valid(), Botan::TLS::Session_Manager::remove(), Botan::TLS::Alert::serialize(), session_manager(), and Botan::TLS::Alert::type().
◆ send_fatal_alert()
|
inlineinherited |
Send a fatal alert
Definition at line 71 of file tls_channel_impl.h.
References Botan::TLS::Alert, and send_alert().
Referenced by Botan::TLS::Channel_Impl_12::from_peer(), and Botan::TLS::Channel_Impl_13::from_peer().
◆ send_new_session_tickets()
|
inlinevirtualinherited |
Send tickets new session tickets to the peer. This is only supported on TLS 1.3 servers.
If the server's Session_Manager does not accept the generated Session objects, the server implementation won't be able to send new tickets. Additionally, anything but TLS 1.3 servers will return 0 (because they don't support sending such session tickets).
- Returns
- the number of session tickets successfully sent to the client
Reimplemented in Botan::TLS::Server_Impl_13.
Definition at line 153 of file tls_channel_impl.h.
◆ send_warning_alert()
|
inlineinherited |
Send a warning alert
Definition at line 66 of file tls_channel_impl.h.
References Botan::TLS::Alert, and send_alert().
Referenced by close().
◆ session_manager()
|
inlineprotectedinherited |
Definition at line 181 of file tls_channel_impl_12.h.
Referenced by Channel_Impl_12(), Botan::TLS::Client_Impl_12::Client_Impl_12(), Botan::TLS::Client_Impl_12::Client_Impl_12(), send_alert(), Botan::TLS::Server_Impl_12::Server_Impl_12(), and Botan::TLS::Server_Impl_12::Server_Impl_12().
◆ set_io_buffer_size()
|
inlineprotectedinherited |
Definition at line 237 of file tls_channel_impl.h.
References BOTAN_STATE_CHECK, and m_downgrade_info.
◆ timeout_check()
|
overridevirtualinherited |
Perform a handshake timeout check. This does nothing unless this is a DTLS channel with a pending handshake state, in which case we check for timeout and potentially retransmit handshake packets.
Implements Botan::TLS::Channel_Impl.
Definition at line 173 of file tls_channel_impl_12.cpp.
◆ to_peer()
|
overridevirtualinherited |
Inject plaintext intended for counterparty Throws an exception if is_active() is false
Implements Botan::TLS::Channel_Impl.
Definition at line 552 of file tls_channel_impl_12.cpp.
References Botan::TLS::ApplicationData, and is_active().
◆ update_traffic_keys()
|
overridevirtualinherited |
Attempt to update the session's traffic key material Note that this is possible with a TLS 1.3 channel, only.
- Parameters
-
request_peer_update if true, require a reciprocal key update
Implements Botan::TLS::Channel_Impl.
Definition at line 198 of file tls_channel_impl_12.cpp.
Member Data Documentation
◆ m_downgrade_info
|
protectedinherited |
Definition at line 222 of file tls_channel_impl.h.
Referenced by Botan::TLS::Channel_Impl_13::expect_downgrade(), expects_downgrade(), extract_downgrade_info(), Botan::TLS::Channel_Impl_13::from_peer(), is_downgrading(), preserve_client_hello(), preserve_peer_transcript(), request_downgrade(), request_downgrade_for_resumption(), and set_io_buffer_size().
The documentation for this class was generated from the following files:
- src/lib/tls/tls12/tls_server_impl_12.h
- src/lib/tls/tls12/tls_server_impl_12.cpp
Generated by