#include <tls_messages_12.h>
Classes | |
| class | Settings |
Public Member Functions | |
| std::vector< Signature_Scheme > | certificate_signature_schemes () const |
| const std::vector< uint16_t > & | ciphersuites () const |
| Client_Hello_12 (const std::vector< uint8_t > &buf) | |
| Client_Hello_12 (Handshake_IO &io, Handshake_Hash &hash, const Policy &policy, Callbacks &cb, RandomNumberGenerator &rng, const std::vector< uint8_t > &reneg_info, const Session_with_Handle &session_and_handle, const std::vector< std::string > &next_protocols) | |
| Client_Hello_12 (Handshake_IO &io, Handshake_Hash &hash, const Policy &policy, Callbacks &cb, RandomNumberGenerator &rng, const std::vector< uint8_t > &reneg_info, const Settings &client_settings, const std::vector< std::string > &next_protocols) | |
| const std::vector< uint8_t > & | compression_methods () const |
| const std::vector< uint8_t > & | cookie () const |
| std::vector< uint8_t > | cookie_input_data () const |
| std::set< Extension_Code > | extension_types () const |
| const Extensions & | extensions () const |
| Protocol_Version | legacy_version () const |
| std::vector< std::string > | next_protocols () const |
| bool | offered_suite (uint16_t ciphersuite) const |
| bool | prefers_compressed_ec_points () const |
| const std::vector< uint8_t > & | random () const |
| std::vector< uint8_t > | renegotiation_info () const |
| bool | secure_renegotiation () const |
| bool | sent_signature_algorithms () const |
| std::vector< uint8_t > | serialize () const override |
| std::optional< Session_Handle > | session_handle () const |
| const Session_ID & | session_id () const |
| Session_Ticket | session_ticket () const |
| std::vector< Signature_Scheme > | signature_schemes () const |
| std::string | sni_hostname () const |
| std::vector< uint16_t > | srtp_profiles () const |
| std::vector< Group_Params > | supported_dh_groups () const |
| std::vector< Group_Params > | supported_ecc_curves () const |
| std::vector< Protocol_Version > | supported_versions () const |
| bool | supports_alpn () const |
| bool | supports_cert_status_message () const |
| bool | supports_encrypt_then_mac () const |
| bool | supports_extended_master_secret () const |
| bool | supports_session_ticket () const |
| Handshake_Type | type () const override |
| std::string | type_string () const |
| void | update_hello_cookie (const Hello_Verify_Request &hello_verify) |
| virtual Handshake_Type | wire_type () const |
Protected Member Functions | |
| Client_Hello () | |
| Client_Hello (Client_Hello &&) noexcept | |
| Client_Hello (const Client_Hello &)=delete | |
| Client_Hello (std::unique_ptr< Client_Hello_Internal > data) | |
Protected Attributes | |
| std::unique_ptr< Client_Hello_Internal > | m_data |
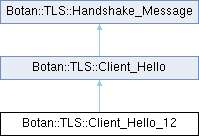
Detailed Description
Definition at line 21 of file tls_messages_12.h.
Constructor & Destructor Documentation
◆ Client_Hello_12() [1/3]
| Botan::TLS::Client_Hello_12::Client_Hello_12 | ( | Handshake_IO & | io, |
| Handshake_Hash & | hash, | ||
| const Policy & | policy, | ||
| Callbacks & | cb, | ||
| RandomNumberGenerator & | rng, | ||
| const std::vector< uint8_t > & | reneg_info, | ||
| const Settings & | client_settings, | ||
| const std::vector< std::string > & | next_protocols ) |
Definition at line 111 of file msg_client_hello_12.cpp.
References Botan::TLS::Policy::acceptable_certificate_signature_schemes(), Botan::TLS::Policy::acceptable_protocol_version(), Botan::TLS::Policy::acceptable_signature_schemes(), Botan::TLS::Policy::ciphersuite_list(), Botan::TLS::Client, Botan::TLS::Client_Hello_12::Settings::hostname(), Botan::TLS::Server_Name_Indicator::hostname_acceptable_for_sni(), Botan::TLS::Client_Hello::m_data, Botan::TLS::make_hello_random(), Botan::TLS::Policy::negotiate_encrypt_then_mac(), Botan::TLS::Client_Hello::next_protocols(), Botan::TLS::Client_Hello_12::Settings::protocol_version(), Botan::TLS::Handshake_IO::send(), Botan::TLS::Policy::srtp_profiles(), Botan::TLS::Policy::support_cert_status_message(), Botan::TLS::Callbacks::tls_modify_extensions(), Botan::TLS::Client_Hello::type(), and Botan::TLS::Handshake_Hash::update().
Referenced by Client_Hello_12().
◆ Client_Hello_12() [2/3]
| Botan::TLS::Client_Hello_12::Client_Hello_12 | ( | Handshake_IO & | io, |
| Handshake_Hash & | hash, | ||
| const Policy & | policy, | ||
| Callbacks & | cb, | ||
| RandomNumberGenerator & | rng, | ||
| const std::vector< uint8_t > & | reneg_info, | ||
| const Session_with_Handle & | session_and_handle, | ||
| const std::vector< std::string > & | next_protocols ) |
Definition at line 186 of file msg_client_hello_12.cpp.
References Botan::TLS::Policy::acceptable_certificate_signature_schemes(), Botan::TLS::Policy::acceptable_protocol_version(), Botan::TLS::Policy::acceptable_signature_schemes(), Botan::TLS::Session_Base::ciphersuite_code(), Botan::TLS::Policy::ciphersuite_list(), Botan::TLS::Client, Botan::TLS::Session_with_Handle::handle, Botan::TLS::Server_Information::hostname(), Botan::TLS::Server_Name_Indicator::hostname_acceptable_for_sni(), Botan::TLS::Session_Handle::id(), Botan::TLS::Session_Handle::is_ticket(), Botan::TLS::Client_Hello::m_data, Botan::TLS::make_hello_random(), Botan::TLS::Client_Hello::next_protocols(), Botan::TLS::Handshake_IO::send(), Botan::TLS::Session_Base::server_info(), Botan::TLS::Session_with_Handle::session, Botan::TLS::Policy::support_cert_status_message(), Botan::TLS::Session_Base::supports_encrypt_then_mac(), Botan::TLS::Session_Handle::ticket(), Botan::TLS::Callbacks::tls_modify_extensions(), Botan::TLS::Client_Hello::type(), Botan::TLS::Handshake_Hash::update(), Botan::value_exists(), and Botan::TLS::Session_Base::version().
◆ Client_Hello_12() [3/3]
|
explicit |
Definition at line 265 of file msg_client_hello_12.cpp.
References Client_Hello_12().
Member Function Documentation
◆ certificate_signature_schemes()
|
inherited |
Definition at line 221 of file msg_client_hello.cpp.
References m_data, and signature_schemes().
Referenced by ~Client_Hello().
◆ ciphersuites()
|
inherited |
Definition at line 157 of file msg_client_hello.cpp.
References m_data.
Referenced by ~Client_Hello().
◆ Client_Hello() [1/4]
|
protectedinherited |
Definition at line 142 of file msg_client_hello.cpp.
References Botan::TLS::Client_Hello::m_data.
◆ Client_Hello() [2/4]
|
protecteddefaultnoexceptinherited |
◆ Client_Hello() [3/4]
|
protecteddeleteinherited |
Referenced by Client_Hello_12_Shim().
◆ Client_Hello() [4/4]
|
explicitprotectedinherited |
Definition at line 143 of file msg_client_hello.cpp.
◆ compression_methods()
| const std::vector< uint8_t > & Botan::TLS::Client_Hello::compression_methods | ( | ) | const |
Definition at line 145 of file msg_client_hello.cpp.
References Botan::TLS::Client_Hello::m_data.
◆ cookie()
|
inherited |
Definition at line 283 of file msg_client_hello.cpp.
References m_data.
Referenced by ~Client_Hello().
◆ cookie_input_data()
|
inherited |
Definition at line 200 of file msg_client_hello.cpp.
References BOTAN_STATE_CHECK, and m_data.
Referenced by ~Client_Hello().
◆ extension_types()
|
inherited |
Definition at line 161 of file msg_client_hello.cpp.
References m_data.
Referenced by Botan::TLS::Server_Hello_12::Server_Hello_12(), Botan::TLS::Client_Hello_13::validate_updates(), and ~Client_Hello().
◆ extensions()
|
inherited |
Definition at line 165 of file msg_client_hello.cpp.
References m_data.
Referenced by Botan::TLS::Certificate_13::Certificate_13(), Botan::TLS::Server_Hello_13::create(), Botan::TLS::Encrypted_Extensions::Encrypted_Extensions(), Botan::TLS::Hello_Retry_Request::Hello_Retry_Request(), Botan::TLS::Server_Hello_13::Server_Hello_13(), Botan::TLS::Client_Hello_13::validate_updates(), and ~Client_Hello().
◆ legacy_version()
|
inherited |
Return the version indicated in the ClientHello. This may differ from the version indicated in the supported_versions extension.
See RFC 8446 4.1.2: TLS 1.3, the client indicates its version preferences in the "supported_versions" extension (Section 4.2.1) and the legacy_version field MUST be set to 0x0303, which is the version number for TLS 1.2.
Definition at line 141 of file msg_client_hello.cpp.
Referenced by ~Client_Hello().
◆ next_protocols()
|
inherited |
Definition at line 269 of file msg_client_hello.cpp.
References m_data.
Referenced by Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_13::Client_Hello_13(), and ~Client_Hello().
◆ offered_suite()
|
inherited |
Definition at line 209 of file msg_client_hello.cpp.
References m_data.
Referenced by ~Client_Hello().
◆ prefers_compressed_ec_points()
| bool Botan::TLS::Client_Hello_12::prefers_compressed_ec_points | ( | ) | const |
Definition at line 29 of file msg_client_hello_12.cpp.
References Botan::TLS::Client_Hello::m_data.
◆ random()
| const std::vector< uint8_t > & Botan::TLS::Client_Hello::random | ( | ) | const |
Definition at line 103 of file msg_client_hello.cpp.
References Botan::TLS::Protocol_Version::is_datagram_protocol(), and Botan::TLS::Client_Hello_Internal::m_legacy_version.
◆ renegotiation_info()
| std::vector< uint8_t > Botan::TLS::Client_Hello_12::renegotiation_info | ( | ) | const |
Definition at line 40 of file msg_client_hello_12.cpp.
References Botan::TLS::Client_Hello::m_data.
Referenced by Botan::TLS::Channel_Impl_12::secure_renegotiation_check().
◆ secure_renegotiation()
| bool Botan::TLS::Client_Hello_12::secure_renegotiation | ( | ) | const |
Definition at line 36 of file msg_client_hello_12.cpp.
References Botan::TLS::Client_Hello::m_data.
Referenced by Botan::TLS::Channel_Impl_12::secure_renegotiation_check(), and Botan::TLS::Server_Hello_12::Server_Hello_12().
◆ sent_signature_algorithms()
|
inherited |
Definition at line 265 of file msg_client_hello.cpp.
References m_data.
Referenced by ~Client_Hello().
◆ serialize()
|
overridevirtualinherited |
- Returns
- DER representation of this message
Implements Botan::TLS::Handshake_Message.
Definition at line 172 of file msg_client_hello.cpp.
References Botan::TLS::append_tls_length_value(), Botan::TLS::Client, and m_data.
Referenced by ~Client_Hello().
◆ session_handle()
| std::optional< Session_Handle > Botan::TLS::Client_Hello_12::session_handle | ( | ) | const |
Definition at line 58 of file msg_client_hello_12.cpp.
References Botan::detail::Container_Strong_Adapter_Base< T >::empty(), Botan::TLS::Client_Hello::session_id(), and session_ticket().
◆ session_id()
|
inherited |
Definition at line 149 of file msg_client_hello.cpp.
References m_data.
Referenced by Botan::TLS::Client_Hello_12::session_handle(), and ~Client_Hello().
◆ session_ticket()
| Session_Ticket Botan::TLS::Client_Hello_12::session_ticket | ( | ) | const |
Definition at line 51 of file msg_client_hello_12.cpp.
References Botan::TLS::Client_Hello::m_data.
Referenced by session_handle(), and Botan::TLS::Handshake_State::session_ticket().
◆ signature_schemes()
|
inherited |
Definition at line 214 of file msg_client_hello.cpp.
References m_data.
Referenced by Botan::TLS::Certificate_13::Certificate_13(), certificate_signature_schemes(), Botan::TLS::Handshake_State::choose_sig_format(), and ~Client_Hello().
◆ sni_hostname()
|
inherited |
Definition at line 247 of file msg_client_hello.cpp.
References m_data.
Referenced by Botan::TLS::Certificate_13::Certificate_13(), Botan::TLS::Certificate_Request_13::maybe_create(), and ~Client_Hello().
◆ srtp_profiles()
|
inherited |
Definition at line 276 of file msg_client_hello.cpp.
References m_data.
Referenced by ~Client_Hello().
◆ supported_dh_groups()
|
inherited |
Definition at line 240 of file msg_client_hello.cpp.
References m_data.
Referenced by ~Client_Hello().
◆ supported_ecc_curves()
|
inherited |
Definition at line 233 of file msg_client_hello.cpp.
References m_data.
Referenced by ~Client_Hello().
◆ supported_versions()
|
inherited |
Definition at line 254 of file msg_client_hello.cpp.
References m_data.
Referenced by ~Client_Hello().
◆ supports_alpn()
|
inherited |
Definition at line 261 of file msg_client_hello.cpp.
References m_data.
Referenced by Botan::TLS::Server_Hello_12::Server_Hello_12(), Botan::TLS::Server_Hello_12::Server_Hello_12(), and ~Client_Hello().
◆ supports_cert_status_message()
| bool Botan::TLS::Client_Hello_12::supports_cert_status_message | ( | ) | const |
Definition at line 76 of file msg_client_hello_12.cpp.
References Botan::TLS::Client_Hello::m_data.
Referenced by Botan::TLS::Server_Hello_12::Server_Hello_12().
◆ supports_encrypt_then_mac()
| bool Botan::TLS::Client_Hello_12::supports_encrypt_then_mac | ( | ) | const |
Definition at line 80 of file msg_client_hello_12.cpp.
References Botan::TLS::Client_Hello::m_data.
Referenced by Botan::TLS::Server_Hello_12::Server_Hello_12(), and Botan::TLS::Server_Hello_12::Server_Hello_12().
◆ supports_extended_master_secret()
| bool Botan::TLS::Client_Hello_12::supports_extended_master_secret | ( | ) | const |
Definition at line 72 of file msg_client_hello_12.cpp.
References Botan::TLS::Client_Hello::m_data.
Referenced by Botan::TLS::Server_Hello_12::Server_Hello_12(), and Botan::TLS::Server_Hello_12::Server_Hello_12().
◆ supports_session_ticket()
| bool Botan::TLS::Client_Hello_12::supports_session_ticket | ( | ) | const |
Definition at line 47 of file msg_client_hello_12.cpp.
References Botan::TLS::Client_Hello::m_data.
Referenced by Botan::TLS::Server_Hello_12::Server_Hello_12().
◆ type()
|
overridevirtualinherited |
- Returns
- the message type
Implements Botan::TLS::Handshake_Message.
Definition at line 137 of file msg_client_hello.cpp.
References Botan::TLS::ClientHello.
Referenced by Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_13::Client_Hello_13(), Botan::TLS::Client_Hello_13::retry(), and ~Client_Hello().
◆ type_string()
|
inherited |
- Returns
- string representation of this message type
Definition at line 21 of file tls_handshake_state.cpp.
References Botan::TLS::handshake_type_to_string(), and type().
◆ update_hello_cookie()
| void Botan::TLS::Client_Hello_12::update_hello_cookie | ( | const Hello_Verify_Request & | hello_verify | ) |
Definition at line 23 of file msg_client_hello_12.cpp.
References BOTAN_STATE_CHECK, Botan::TLS::Hello_Verify_Request::cookie(), and Botan::TLS::Client_Hello::m_data.
◆ wire_type()
|
inlinevirtualinherited |
- Returns
- the wire representation of the message's type
Reimplemented in Botan::TLS::Hello_Retry_Request.
Definition at line 39 of file tls_handshake_msg.h.
References type().
Referenced by Botan::TLS::Stream_Handshake_IO::send().
Member Data Documentation
◆ m_data
|
protectedinherited |
Definition at line 148 of file tls_messages.h.
Referenced by certificate_signature_schemes(), ciphersuites(), Client_Hello(), Client_Hello(), Botan::TLS::Client_Hello_12_Shim::Client_Hello(), Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_13::Client_Hello_13(), compression_methods(), Botan::TLS::Client_Hello_12::compression_methods(), cookie(), cookie_input_data(), extension_types(), extensions(), Botan::TLS::Client_Hello_13::highest_supported_version(), next_protocols(), offered_suite(), Botan::TLS::Client_Hello_12::prefers_compressed_ec_points(), Botan::TLS::Client_Hello_12::renegotiation_info(), Botan::TLS::Client_Hello_13::retry(), Botan::TLS::Client_Hello_12::secure_renegotiation(), sent_signature_algorithms(), serialize(), session_id(), Botan::TLS::Client_Hello_12::session_ticket(), signature_schemes(), sni_hostname(), srtp_profiles(), supported_dh_groups(), supported_ecc_curves(), supported_versions(), supports_alpn(), Botan::TLS::Client_Hello_12::supports_cert_status_message(), Botan::TLS::Client_Hello_12::supports_encrypt_then_mac(), Botan::TLS::Client_Hello_12::supports_extended_master_secret(), Botan::TLS::Client_Hello_12::supports_session_ticket(), Botan::TLS::Client_Hello_12::update_hello_cookie(), and Botan::TLS::Client_Hello_13::validate_updates().
The documentation for this class was generated from the following files:
- src/lib/tls/tls12/tls_messages_12.h
- src/lib/tls/tls12/msg_client_hello_12.cpp
Generated by