#include <x509cert.h>
Classes | |
| class | Tag |
| class | TagHash |
Public Member Functions | |
| bool | allowed_extended_usage (const OID &usage) const |
| bool | allowed_extended_usage (std::string_view usage) const |
| bool | allowed_usage (Key_Constraints usage) const |
| bool | allowed_usage (Usage_Type usage) const |
| const std::vector< uint8_t > & | authority_key_id () const |
| std::vector< uint8_t > | BER_encode () const |
| std::vector< std::string > | ca_issuers () const |
| std::span< const uint8_t, 20 > | certificate_data_sha1 () const |
| std::span< const uint8_t, 32 > | certificate_data_sha256 () const |
| const std::vector< OID > & | certificate_policy_oids () const |
| bool | check_signature (const Public_Key &key) const |
| Key_Constraints | constraints () const |
| std::string | crl_distribution_point () const |
| std::vector< std::string > | crl_distribution_points () const |
| void | decode_from (BER_Decoder &from) override |
| void | encode_into (DER_Encoder &to) const override |
| const std::vector< OID > & | extended_key_usage () const |
| std::string | fingerprint (std::string_view hash_name="SHA-1") const |
| bool | has_constraints (Key_Constraints constraints) const |
| bool | has_ex_constraint (const OID &ex_constraint) const |
| bool | has_ex_constraint (std::string_view ex_constraint) const |
| bool | is_CA_cert () const |
| bool | is_critical (std::string_view ex_name) const |
| bool | is_self_signed () const |
| bool | is_serial_negative () const |
| const AlternativeName & | issuer_alt_name () const |
| const X509_DN & | issuer_dn () const |
| std::vector< std::string > | issuer_info (std::string_view name) const |
| std::unique_ptr< Public_Key > | load_subject_public_key () const |
| bool | matches_dns_name (std::string_view name) const |
| const NameConstraints & | name_constraints () const |
| const X509_Time & | not_after () const |
| const X509_Time & | not_before () const |
| std::string | ocsp_responder () const |
| const std::vector< std::string > & | ocsp_responders () const |
| bool | operator< (const X509_Certificate &other) const |
| X509_Certificate & | operator= (const X509_Certificate &other)=default |
| X509_Certificate & | operator= (X509_Certificate &&other)=default |
| bool | operator== (const X509_Certificate &other) const |
| std::optional< size_t > | path_length_constraint () const |
| uint32_t | path_limit () const |
| std::string | PEM_encode () const |
| const std::vector< uint8_t > & | raw_issuer_dn () const |
| const std::vector< uint8_t > & | raw_issuer_dn_sha256 () const |
| const std::vector< uint8_t > & | raw_subject_dn () const |
| const std::vector< uint8_t > & | raw_subject_dn_sha256 () const |
| const std::vector< uint8_t > & | serial_number () const |
| const std::vector< uint8_t > & | signature () const |
| const AlgorithmIdentifier & | signature_algorithm () const |
| const std::vector< uint8_t > & | signed_body () const |
| const AlternativeName & | subject_alt_name () const |
| const X509_DN & | subject_dn () const |
| std::vector< std::string > | subject_info (std::string_view name) const |
| const std::vector< uint8_t > & | subject_key_id () const |
| std::unique_ptr< Public_Key > | subject_public_key () const |
| const AlgorithmIdentifier & | subject_public_key_algo () const |
| const std::vector< uint8_t > & | subject_public_key_bits () const |
| const std::vector< uint8_t > & | subject_public_key_bitstring () const |
| const std::vector< uint8_t > & | subject_public_key_bitstring_sha1 () const |
| const std::vector< uint8_t > & | subject_public_key_info () const |
| Tag | tag () const |
| std::vector< uint8_t > | tbs_data () const |
| std::string | to_string () const |
| const std::vector< uint8_t > & | v2_issuer_key_id () const |
| const std::vector< uint8_t > & | v2_subject_key_id () const |
| const Extensions & | v3_extensions () const |
| std::pair< Certificate_Status_Code, std::string > | verify_signature (const Public_Key &key) const |
| X509_Certificate ()=default | |
| X509_Certificate (const uint8_t data[], size_t length) | |
| X509_Certificate (const X509_Certificate &other)=default | |
| X509_Certificate (DataSource &source) | |
| X509_Certificate (std::span< const uint8_t > in) | |
| X509_Certificate (X509_Certificate &&other)=default | |
| uint32_t | x509_version () const |
| ~X509_Certificate () override | |
Static Public Member Functions | |
| static std::unique_ptr< PK_Signer > | choose_sig_format (const Private_Key &key, RandomNumberGenerator &rng, std::string_view hash_fn, std::string_view padding_algo) |
| static std::vector< uint8_t > | make_signed (PK_Signer &signer, RandomNumberGenerator &rng, const AlgorithmIdentifier &alg_id, std::span< const uint8_t > tbs) |
Protected Member Functions | |
| void | load_data (DataSource &src) |
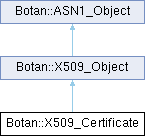
Detailed Description
This class represents an X.509 Certificate
TODO(Botan4) mark this final once PKCS11_X509_Certificate is fixed
Definition at line 32 of file x509cert.h.
Constructor & Destructor Documentation
◆ X509_Certificate() [1/6]
|
explicit |
Create a certificate from a data source providing the DER or PEM encoded certificate.
- Parameters
-
source the data source
Definition at line 86 of file x509cert.cpp.
References Botan::X509_Object::load_data().
Referenced by operator<(), operator=(), operator=(), operator==(), X509_Certificate(), X509_Certificate(), and X509_Certificate().
◆ X509_Certificate() [2/6]
|
explicit |
Create a certificate from a buffer
- Parameters
-
in the buffer containing the DER-encoded certificate
Definition at line 90 of file x509cert.cpp.
References Botan::X509_Object::load_data().
◆ X509_Certificate() [3/6]
|
inline |
Create a certificate from a buffer
- Parameters
-
data the buffer containing the DER-encoded certificate length length of data in bytes
Definition at line 469 of file x509cert.h.
References X509_Certificate().
◆ X509_Certificate() [4/6]
|
default |
Create an uninitialized certificate object. Any attempts to access this object will throw an exception.
◆ X509_Certificate() [5/6]
|
default |
References X509_Certificate().
◆ X509_Certificate() [6/6]
|
default |
References X509_Certificate().
◆ ~X509_Certificate()
|
overridedefault |
Member Function Documentation
◆ allowed_extended_usage() [1/2]
| bool Botan::X509_Certificate::allowed_extended_usage | ( | const OID & | usage | ) | const |
Returns true if the specified usage is set in the extended key usage extension, or if no extended key usage constraints are set at all. To check if a certain extended key constraint is set in the certificate use
- See also
- X509_Certificate::has_ex_constraint.
Definition at line 497 of file x509cert.cpp.
References extended_key_usage(), and has_ex_constraint().
◆ allowed_extended_usage() [2/2]
| bool Botan::X509_Certificate::allowed_extended_usage | ( | std::string_view | usage | ) | const |
Returns true if the specified
- Parameters
-
usage is set in the extended key usage extension or if no extended key usage constraints are set at all. To check if a certain extended key constraint is set in the certificate use
- See also
- X509_Certificate::has_ex_constraint.
Definition at line 493 of file x509cert.cpp.
References allowed_extended_usage(), and Botan::OID::from_string().
Referenced by allowed_extended_usage(), and allowed_usage().
◆ allowed_usage() [1/2]
| bool Botan::X509_Certificate::allowed_usage | ( | Key_Constraints | usage | ) | const |
Returns true if the specified
- Parameters
-
usage is set in the key usage extension or if no key usage constraints are set at all. To check if a certain key constraint is set in the certificate use
- See also
- X509_Certificate::has_constraints.
Definition at line 486 of file x509cert.cpp.
References constraints(), and Botan::Key_Constraints::includes().
Referenced by allowed_usage(), and Botan::PKIX::check_crl().
◆ allowed_usage() [2/2]
| bool Botan::X509_Certificate::allowed_usage | ( | Usage_Type | usage | ) | const |
Returns true if the required key and extended key constraints are set in the certificate for the specified
- Parameters
-
usage or if no key constraints are set in both the key usage and extended key usage extension.
Definition at line 510 of file x509cert.cpp.
References allowed_extended_usage(), allowed_usage(), Botan::CERTIFICATE_AUTHORITY, Botan::Key_Constraints::DataEncipherment, Botan::Key_Constraints::DigitalSignature, Botan::ENCRYPTION, has_ex_constraint(), is_CA_cert(), Botan::Key_Constraints::KeyAgreement, Botan::Key_Constraints::KeyEncipherment, Botan::Key_Constraints::NonRepudiation, Botan::OCSP_RESPONDER, Botan::TLS_CLIENT_AUTH, Botan::TLS_SERVER_AUTH, and Botan::UNSPECIFIED.
◆ authority_key_id()
| const std::vector< uint8_t > & Botan::X509_Certificate::authority_key_id | ( | ) | const |
Get the DER encoded AuthorityKeyIdentifier of this certificate.
- Returns
- DER encoded AuthorityKeyIdentifier
Definition at line 398 of file x509cert.cpp.
Referenced by botan_x509_cert_view_binary_values(), Botan::Certificate_Store_In_Memory::find_crl_for(), Botan::X509_CRL::is_revoked(), and to_string().
◆ BER_encode()
|
inherited |
Return the encoding of this object. This is a convenience method when just one object needs to be serialized. Use DER_Encoder for complicated encodings.
Definition at line 20 of file asn1_obj.cpp.
References encode_into().
Referenced by decode_from(), Botan::Certificate_Store_In_SQL::find_all_certs(), Botan::Certificate_Store_In_SQL::find_cert(), Botan::X509_Certificate::fingerprint(), Botan::Certificate_Store_In_SQL::insert_cert(), Botan::X509_Object::PEM_encode(), Botan::PSS_Params::PSS_Params(), and Botan::Certificate_Store_In_SQL::revoke_cert().
◆ ca_issuers()
| std::vector< std::string > Botan::X509_Certificate::ca_issuers | ( | ) | const |
Return the listed addresses of ca issuers, or empty if not set
Definition at line 586 of file x509cert.cpp.
Referenced by to_string().
◆ certificate_data_sha1()
| std::span< const uint8_t, 20 > Botan::X509_Certificate::certificate_data_sha1 | ( | ) | const |
SHA-1 of the entire certificate DER encoding
Definition at line 430 of file x509cert.cpp.
◆ certificate_data_sha256()
| std::span< const uint8_t, 32 > Botan::X509_Certificate::certificate_data_sha256 | ( | ) | const |
SHA-256 of the entire certificate DER encoding
Definition at line 437 of file x509cert.cpp.
◆ certificate_policy_oids()
| const std::vector< OID > & Botan::X509_Certificate::certificate_policy_oids | ( | ) | const |
Get the policies as defined in the CertificatePolicies extension of this certificate.
- Returns
- certificate policies
Definition at line 469 of file x509cert.cpp.
Referenced by to_string().
◆ check_signature()
|
inherited |
Check the signature on this data
- Parameters
-
key the public key purportedly used to sign this data
- Returns
- true if the signature is valid, otherwise false
Definition at line 125 of file x509_obj.cpp.
References Botan::VERIFIED, and verify_signature().
◆ choose_sig_format()
|
staticinherited |
Choose and return a signature scheme appropriate for X.509 signing using the provided parameters.
- Parameters
-
key will be the key to choose a padding scheme for Random Number Generators the random generator to use hash_fn is the desired hash function padding_algo specifies the padding method
- Returns
- a PK_Signer object for generating signatures
Definition at line 237 of file x509_obj.cpp.
References Botan::Asymmetric_Key::_default_x509_signature_format(), and Botan::Asymmetric_Key::algo_name().
Referenced by Botan::PKCS10_Request::create(), Botan::X509::create_self_signed_cert(), and Botan::X509_CA::X509_CA().
◆ constraints()
| Key_Constraints Botan::X509_Certificate::constraints | ( | ) | const |
Get the key constraints as defined in the KeyUsage extension of this certificate.
- Returns
- key constraints
Definition at line 461 of file x509cert.cpp.
Referenced by allowed_usage(), has_constraints(), and to_string().
◆ crl_distribution_point()
| std::string Botan::X509_Certificate::crl_distribution_point | ( | ) | const |
Return the CRL distribution point, or empty if not set
Definition at line 594 of file x509cert.cpp.
◆ crl_distribution_points()
| std::vector< std::string > Botan::X509_Certificate::crl_distribution_points | ( | ) | const |
Return the CRL distribution points, or empty if not set
Definition at line 590 of file x509cert.cpp.
Referenced by to_string().
◆ decode_from()
|
overridevirtualinherited |
Decode a BER encoded X509_Object See ASN1_Object::decode_from()
Implements Botan::ASN1_Object.
Definition at line 93 of file x509_obj.cpp.
References Botan::BitString, Botan::BER_Decoder::decode(), Botan::BER_Decoder::end_cons(), Botan::BER_Decoder::raw_bytes(), and Botan::BER_Decoder::start_sequence().
Referenced by load_data().
◆ encode_into()
|
overridevirtualinherited |
DER encode an X509_Object See ASN1_Object::encode_into()
Implements Botan::ASN1_Object.
Definition at line 80 of file x509_obj.cpp.
References Botan::BitString, Botan::DER_Encoder::encode(), Botan::DER_Encoder::end_cons(), Botan::DER_Encoder::raw_bytes(), signature(), signature_algorithm(), signed_body(), and Botan::DER_Encoder::start_sequence().
◆ extended_key_usage()
| const std::vector< OID > & Botan::X509_Certificate::extended_key_usage | ( | ) | const |
Get the key usage as defined in the ExtendedKeyUsage extension of this certificate, or else an empty vector.
- Returns
- key usage
Definition at line 465 of file x509cert.cpp.
Referenced by allowed_extended_usage(), has_ex_constraint(), and to_string().
◆ fingerprint()
| std::string Botan::X509_Certificate::fingerprint | ( | std::string_view | hash_name = "SHA-1" | ) | const |
- Returns
- a fingerprint of the certificate
- Parameters
-
hash_name hash function used to calculate the fingerprint
Definition at line 685 of file x509cert.cpp.
References Botan::ASN1_Object::BER_encode(), and Botan::create_hex_fingerprint().
Referenced by Botan::Certificate_Store_In_SQL::affirm_cert(), Botan::Certificate_Store_In_SQL::contains(), Botan::Certificate_Store_In_SQL::find_key(), Botan::Certificate_Store_In_SQL::insert_cert(), Botan::Certificate_Store_In_SQL::insert_key(), Botan::Certificate_Store_In_SQL::remove_cert(), Botan::Certificate_Store_In_SQL::revoke_cert(), and Botan::Certificate_Store_In_SQL::revoke_cert().
◆ has_constraints()
| bool Botan::X509_Certificate::has_constraints | ( | Key_Constraints | constraints | ) | const |
Returns true if and only if the specified
- Parameters
-
constraints are included in the key usage extension.
Typically for applications you want allowed_usage instead.
Definition at line 481 of file x509cert.cpp.
References constraints(), and Botan::Key_Constraints::includes().
◆ has_ex_constraint() [1/2]
| bool Botan::X509_Certificate::has_ex_constraint | ( | const OID & | ex_constraint | ) | const |
Returns true if and only if OID
- Parameters
-
ex_constraint is included in the extended key extension.
Definition at line 544 of file x509cert.cpp.
References extended_key_usage(), and Botan::OID::from_name().
◆ has_ex_constraint() [2/2]
| bool Botan::X509_Certificate::has_ex_constraint | ( | std::string_view | ex_constraint | ) | const |
Returns true if and only if OID
- Parameters
-
ex_constraint is included in the extended key extension.
Definition at line 540 of file x509cert.cpp.
References Botan::OID::from_string(), and has_ex_constraint().
Referenced by allowed_extended_usage(), allowed_usage(), and has_ex_constraint().
◆ is_CA_cert()
| bool Botan::X509_Certificate::is_CA_cert | ( | ) | const |
Check whether this certificate is a CA certificate.
- Returns
- true if this certificate is a CA certificate
Definition at line 441 of file x509cert.cpp.
Referenced by allowed_usage(), Botan::Flatfile_Certificate_Store::Flatfile_Certificate_Store(), and Botan::Cert_Extension::Name_Constraints::validate().
◆ is_critical()
| bool Botan::X509_Certificate::is_critical | ( | std::string_view | ex_name | ) | const |
Check whenever a given X509 Extension is marked critical in this certificate.
Definition at line 571 of file x509cert.cpp.
References Botan::Extensions::critical_extension_set(), Botan::OID::from_string(), and v3_extensions().
Referenced by Botan::Cert_Extension::Name_Constraints::validate().
◆ is_self_signed()
| bool Botan::X509_Certificate::is_self_signed | ( | ) | const |
Check whether this certificate is self signed. If the DN issuer and subject agree,
- Returns
- true if this certificate is self signed
Definition at line 354 of file x509cert.cpp.
Referenced by Botan::PKIX::check_chain(), Botan::Flatfile_Certificate_Store::Flatfile_Certificate_Store(), and to_string().
◆ is_serial_negative()
| bool Botan::X509_Certificate::is_serial_negative | ( | ) | const |
Get the serial number's sign
- Returns
- 1 iff the serial is negative.
Definition at line 410 of file x509cert.cpp.
Referenced by Botan::PKIX::check_chain().
◆ issuer_alt_name()
| const AlternativeName & Botan::X509_Certificate::issuer_alt_name | ( | ) | const |
Return the issuer alternative names (DNS, IP, ...)
Definition at line 606 of file x509cert.cpp.
Referenced by botan_x509_cert_issuer_alternative_names(), botan_x509_cert_issuer_alternative_names_count(), and issuer_info().
◆ issuer_dn()
| const X509_DN & Botan::X509_Certificate::issuer_dn | ( | ) | const |
Get the certificate's issuer distinguished name (DN).
- Returns
- issuer DN of this certificate
Definition at line 414 of file x509cert.cpp.
Referenced by Botan::PKIX::check_chain(), Botan::Certificate_Store_In_Memory::find_crl_for(), Botan::Certificate_Store_In_SQL::find_crl_for(), Botan::Flatfile_Certificate_Store::Flatfile_Certificate_Store(), Botan::X509_CRL::is_revoked(), issuer_info(), Botan::OCSP::Request::Request(), and to_string().
◆ issuer_info()
| std::vector< std::string > Botan::X509_Certificate::issuer_info | ( | std::string_view | name | ) | const |
Get a value for a specific subject_info parameter name.
- Parameters
-
name the name of the parameter to look up. Possible names are "X509.Certificate.v2.key_id" or "X509v3.AuthorityKeyIdentifier".
- Returns
- value(s) of the specified parameter
Definition at line 652 of file x509cert.cpp.
References issuer_alt_name(), and issuer_dn().
◆ load_data()
|
protectedinherited |
Decodes from src as either DER or PEM data, then calls force_decode()
Definition at line 24 of file x509_obj.cpp.
References alternate_PEM_labels(), Botan::PEM_Code::decode(), decode_from(), Botan::BER_Decoder::Limits::DER(), Botan::PEM_Code::matches(), Botan::ASN1::maybe_BER(), and PEM_label().
Referenced by Botan::PKCS10_Request::PKCS10_Request(), Botan::PKCS10_Request::PKCS10_Request(), Botan::X509_Certificate::X509_Certificate(), Botan::X509_Certificate::X509_Certificate(), Botan::X509_CRL::X509_CRL(), Botan::X509_CRL::X509_CRL(), and X509_Object().
◆ load_subject_public_key()
| std::unique_ptr< Public_Key > Botan::X509_Certificate::load_subject_public_key | ( | ) | const |
Create a public key object associated with the public key bits in this certificate. If the public key bits was valid for X.509 encoding purposes but invalid algorithmically (for example, RSA with an even modulus) that will be detected at this point, and an exception will be thrown.
- Returns
- subject public key of this certificate
Definition at line 667 of file x509cert.cpp.
References subject_public_key().
◆ make_signed()
|
staticinherited |
Create a signed X509 object.
- Parameters
-
signer the signer used to sign the object Random Number Generators the random number generator to use alg_id the algorithm identifier of the signature scheme tbs the tbs bits to be signed
- Returns
- signed X509 object
Definition at line 153 of file x509_obj.cpp.
References Botan::BitString, Botan::DER_Encoder::encode(), Botan::DER_Encoder::end_cons(), Botan::DER_Encoder::raw_bytes(), Botan::PK_Signer::sign_message(), signature(), and Botan::DER_Encoder::start_sequence().
Referenced by Botan::PKCS10_Request::create(), and Botan::X509_CA::make_cert().
◆ matches_dns_name()
| bool Botan::X509_Certificate::matches_dns_name | ( | std::string_view | name | ) | const |
Check if a certain DNS name matches up with the information in the cert
- Parameters
-
name DNS name to match
Note: this will also accept a dotted quad input, in which case the SAN for IPv4 addresses will be checked.
Definition at line 708 of file x509cert.cpp.
References Botan::IPv6Address::from_string(), Botan::host_wildcard_match(), Botan::AlternativeName::ipv4_address(), Botan::AlternativeName::ipv6_address(), Botan::string_to_ipv4(), subject_alt_name(), and subject_info().
◆ name_constraints()
| const NameConstraints & Botan::X509_Certificate::name_constraints | ( | ) | const |
Get the name constraints as defined in the NameConstraints extension of this certificate.
- Returns
- name constraints
Definition at line 473 of file x509cert.cpp.
Referenced by botan_x509_cert_excluded_name_constraints(), botan_x509_cert_permitted_name_constraints(), and to_string().
◆ not_after()
| const X509_Time & Botan::X509_Certificate::not_after | ( | ) | const |
Get the notAfter of the certificate as X509_Time
- Returns
- notAfter of the certificate
Definition at line 362 of file x509cert.cpp.
Referenced by Botan::PKIX::check_chain(), and to_string().
◆ not_before()
| const X509_Time & Botan::X509_Certificate::not_before | ( | ) | const |
Get the notBefore of the certificate as X509_Time
- Returns
- notBefore of the certificate
Definition at line 358 of file x509cert.cpp.
Referenced by Botan::PKIX::check_chain(), and to_string().
◆ ocsp_responder()
| std::string Botan::X509_Certificate::ocsp_responder | ( | ) | const |
Return the listed address of an OCSP responder, or empty if not set
Definition at line 575 of file x509cert.cpp.
Referenced by to_string().
◆ ocsp_responders()
| const std::vector< std::string > & Botan::X509_Certificate::ocsp_responders | ( | ) | const |
Return the listed addresses of OCSP responders, or empty if not set
Definition at line 582 of file x509cert.cpp.
Referenced by to_string().
◆ operator<()
| bool Botan::X509_Certificate::operator< | ( | const X509_Certificate & | other | ) | const |
Impose an arbitrary (but consistent) ordering, eg to allow sorting a container of certificate objects.
- Returns
- true if this is less than other by some unspecified criteria
Definition at line 747 of file x509cert.cpp.
References Botan::X509_Object::signature(), Botan::X509_Object::signed_body(), and X509_Certificate().
◆ operator=() [1/2]
|
default |
References X509_Certificate().
◆ operator=() [2/2]
|
default |
References X509_Certificate().
◆ operator==()
| bool Botan::X509_Certificate::operator== | ( | const X509_Certificate & | other | ) | const |
Check to certificates for equality.
- Returns
- true both certificates are (binary) equal
Definition at line 742 of file x509cert.cpp.
References Botan::X509_Object::signature(), Botan::X509_Object::signature_algorithm(), Botan::X509_Object::signed_body(), and X509_Certificate().
◆ path_length_constraint()
| std::optional< size_t > Botan::X509_Certificate::path_length_constraint | ( | ) | const |
Get the path length constraint as defined in the BasicConstraints extension.
Returns nullopt if either the extension is not set in the certificate, or if the pathLenConstraint field was absent from the extension.
- Returns
- path limit
Definition at line 457 of file x509cert.cpp.
Referenced by Botan::PKIX::check_chain().
◆ path_limit()
| uint32_t Botan::X509_Certificate::path_limit | ( | ) | const |
Get the path length constraint as defined in the BasicConstraints extension.
This returns an arbitrary value if the extension is not set (either 32 for v1 self-signed certificates, or else Cert_Extension::NO_CERT_PATH_LIMIT for v3 certificates without the extension)
Prefer path_length_constraint
- Returns
- path limit
Definition at line 449 of file x509cert.cpp.
◆ PEM_encode()
|
inherited |
- Returns
- PEM encoding of this
Definition at line 111 of file x509_obj.cpp.
References Botan::ASN1_Object::BER_encode(), Botan::PEM_Code::encode(), and PEM_label().
◆ raw_issuer_dn()
| const std::vector< uint8_t > & Botan::X509_Certificate::raw_issuer_dn | ( | ) | const |
Raw issuer DN bits
Definition at line 422 of file x509cert.cpp.
Referenced by botan_x509_cert_view_binary_values(), and Botan::OCSP::CertID::is_id_for().
◆ raw_issuer_dn_sha256()
| const std::vector< uint8_t > & Botan::X509_Certificate::raw_issuer_dn_sha256 | ( | ) | const |
SHA-256 of Raw issuer DN
Definition at line 671 of file x509cert.cpp.
◆ raw_subject_dn()
| const std::vector< uint8_t > & Botan::X509_Certificate::raw_subject_dn | ( | ) | const |
Raw subject DN
Definition at line 426 of file x509cert.cpp.
Referenced by botan_x509_cert_view_binary_values(), and Botan::OCSP::CertID::CertID().
◆ raw_subject_dn_sha256()
| const std::vector< uint8_t > & Botan::X509_Certificate::raw_subject_dn_sha256 | ( | ) | const |
SHA-256 of Raw subject DN
Definition at line 678 of file x509cert.cpp.
Referenced by Botan::Flatfile_Certificate_Store::Flatfile_Certificate_Store().
◆ serial_number()
| const std::vector< uint8_t > & Botan::X509_Certificate::serial_number | ( | ) | const |
Get the serial number of this certificate.
- Returns
- certificates serial number
Definition at line 406 of file x509cert.cpp.
Referenced by botan_x509_cert_serial_number(), botan_x509_cert_view_binary_values(), Botan::OCSP::CertID::is_id_for(), Botan::X509_CRL::is_revoked(), and to_string().
◆ signature()
|
inherited |
- Returns
- signature on tbs_data()
Definition at line 59 of file x509_obj.cpp.
Referenced by encode_into(), make_signed(), Botan::X509_Certificate::operator<(), Botan::X509_Certificate::operator==(), and verify_signature().
◆ signature_algorithm()
|
inherited |
- Returns
- signature algorithm that was used to generate signature
Definition at line 73 of file x509_obj.cpp.
Referenced by Botan::PKIX::check_chain(), encode_into(), Botan::X509_Certificate::operator==(), Botan::X509_Certificate::to_string(), and verify_signature().
◆ signed_body()
|
inherited |
- Returns
- signed body
Definition at line 66 of file x509_obj.cpp.
Referenced by encode_into(), Botan::X509_Certificate::operator<(), Botan::X509_Certificate::operator==(), and tbs_data().
◆ subject_alt_name()
| const AlternativeName & Botan::X509_Certificate::subject_alt_name | ( | ) | const |
Return the subject alternative names (DNS, IP, ...)
Definition at line 602 of file x509cert.cpp.
Referenced by botan_x509_cert_subject_alternative_names(), botan_x509_cert_subject_alternative_names_count(), Botan::NameConstraints::is_excluded(), Botan::NameConstraints::is_permitted(), Botan::GeneralName::matches(), matches_dns_name(), and subject_info().
◆ subject_dn()
| const X509_DN & Botan::X509_Certificate::subject_dn | ( | ) | const |
Get the certificate's subject distinguished name (DN).
- Returns
- subject DN of this certificate
Definition at line 418 of file x509cert.cpp.
Referenced by Botan::Certificate_Store_In_Memory::add_certificate(), Botan::PKIX::check_chain(), Botan::Certificate_Store::contains(), Botan::Flatfile_Certificate_Store::Flatfile_Certificate_Store(), Botan::Certificate_Store_In_SQL::insert_cert(), Botan::NameConstraints::is_excluded(), Botan::NameConstraints::is_permitted(), Botan::GeneralName::matches(), Botan::Certificate_Store_In_SQL::remove_cert(), Botan::OCSP::Request::Request(), subject_info(), and to_string().
◆ subject_info()
| std::vector< std::string > Botan::X509_Certificate::subject_info | ( | std::string_view | name | ) | const |
Get a value for a specific subject_info parameter name.
- Parameters
-
name the name of the parameter to look up. Possible names include "X509.Certificate.version", "X509.Certificate.serial", "X509.Certificate.start", "X509.Certificate.end", "X509.Certificate.v2.key_id", "X509.Certificate.public_key", "X509v3.BasicConstraints.path_constraint", "X509v3.BasicConstraints.is_ca", "X509v3.NameConstraints", "X509v3.ExtendedKeyUsage", "X509v3.CertificatePolicies", "X509v3.SubjectKeyIdentifier", "X509.Certificate.serial", "X520.CommonName", "X520.Organization", "X520.Country", "RFC822" (Email in SAN) or "PKCS9.EmailAddress" (Email in DN).
- Returns
- value(s) of the specified parameter
Definition at line 645 of file x509cert.cpp.
References subject_alt_name(), and subject_dn().
Referenced by Botan::NameConstraints::is_excluded(), Botan::NameConstraints::is_permitted(), and matches_dns_name().
◆ subject_key_id()
| const std::vector< uint8_t > & Botan::X509_Certificate::subject_key_id | ( | ) | const |
Get the DER encoded SubjectKeyIdentifier of this certificate.
- Returns
- DER encoded SubjectKeyIdentifier
Definition at line 402 of file x509cert.cpp.
Referenced by botan_x509_cert_view_binary_values(), Botan::Certificate_Store::contains(), Botan::Certificate_Store_In_SQL::insert_cert(), Botan::Certificate_Store_In_SQL::remove_cert(), and to_string().
◆ subject_public_key()
| std::unique_ptr< Public_Key > Botan::X509_Certificate::subject_public_key | ( | ) | const |
Create a public key object associated with the public key bits in this certificate. If the public key bits was valid for X.509 encoding purposes but invalid algorithmically (for example, RSA with an even modulus) that will be detected at this point, and an exception will be thrown.
- Returns
- subject public key of this certificate
Definition at line 659 of file x509cert.cpp.
References Botan::X509::load_key(), and subject_public_key_info().
Referenced by Botan::PKIX::check_chain(), Botan::PKIX::check_crl(), load_subject_public_key(), to_string(), Botan::TLS::Certificate_Verify_12::verify(), and Botan::OCSP::Response::verify_signature().
◆ subject_public_key_algo()
| const AlgorithmIdentifier & Botan::X509_Certificate::subject_public_key_algo | ( | ) | const |
Return the algorithm identifier of the public key
Definition at line 366 of file x509cert.cpp.
Referenced by to_string().
◆ subject_public_key_bits()
| const std::vector< uint8_t > & Botan::X509_Certificate::subject_public_key_bits | ( | ) | const |
Get the public key associated with this certificate. This includes the outer AlgorithmIdentifier
- Returns
- subject public key of this certificate
Definition at line 378 of file x509cert.cpp.
◆ subject_public_key_bitstring()
| const std::vector< uint8_t > & Botan::X509_Certificate::subject_public_key_bitstring | ( | ) | const |
Get the bit string of the public key associated with this certificate
- Returns
- public key bits
Definition at line 386 of file x509cert.cpp.
Referenced by Botan::OCSP::CertID::CertID(), Botan::OCSP::CertID::is_id_for(), and to_string().
◆ subject_public_key_bitstring_sha1()
| const std::vector< uint8_t > & Botan::X509_Certificate::subject_public_key_bitstring_sha1 | ( | ) | const |
Get the SHA-1 bit string of the public key associated with this certificate. This is used for OCSP among other protocols. This function will throw if SHA-1 is not available.
- Returns
- hash of subject public key of this certificate
Definition at line 390 of file x509cert.cpp.
Referenced by Botan::Flatfile_Certificate_Store::Flatfile_Certificate_Store().
◆ subject_public_key_info()
| const std::vector< uint8_t > & Botan::X509_Certificate::subject_public_key_info | ( | ) | const |
Get the SubjectPublicKeyInfo associated with this certificate.
- Returns
- subject public key info of this certificate
Definition at line 382 of file x509cert.cpp.
Referenced by botan_x509_cert_view_binary_values(), and subject_public_key().
◆ tag()
| X509_Certificate::Tag Botan::X509_Certificate::tag | ( | ) | const |
Return a collision resistant binary "tag" of this certificate
Definition at line 704 of file x509cert.cpp.
Referenced by Botan::Certificate_Store_In_Memory::add_certificate(), Botan::Certificate_Store_In_Memory::contains(), Botan::Flatfile_Certificate_Store::contains(), Botan::Flatfile_Certificate_Store::Flatfile_Certificate_Store(), and Botan::X509_Certificate::TagHash::operator()().
◆ tbs_data()
|
inherited |
The underlying data that is to be or was signed
- Returns
- data that is or was signed
Definition at line 118 of file x509_obj.cpp.
References Botan::ASN1::put_in_sequence(), and signed_body().
Referenced by verify_signature().
◆ to_string()
| std::string Botan::X509_Certificate::to_string | ( | ) | const |
- Returns
- a free-form string describing the certificate
Definition at line 764 of file x509cert.cpp.
References authority_key_id(), ca_issuers(), certificate_policy_oids(), constraints(), crl_distribution_points(), Botan::Key_Constraints::CrlSign, Botan::Key_Constraints::DataEncipherment, Botan::Key_Constraints::DecipherOnly, Botan::Key_Constraints::DigitalSignature, Botan::Key_Constraints::empty(), Botan::Key_Constraints::EncipherOnly, extended_key_usage(), Botan::hex_encode(), is_self_signed(), issuer_dn(), Botan::Key_Constraints::KeyAgreement, Botan::Key_Constraints::KeyCertSign, Botan::Key_Constraints::KeyEncipherment, name_constraints(), Botan::Key_Constraints::NonRepudiation, not_after(), not_before(), ocsp_responder(), ocsp_responders(), Botan::AlgorithmIdentifier::oid(), Botan::X509::PEM_encode(), Botan::NameConstraints::permitted(), Botan::ASN1_Time::readable_string(), serial_number(), Botan::X509_Object::signature_algorithm(), subject_dn(), subject_key_id(), subject_public_key(), subject_public_key_algo(), subject_public_key_bitstring(), Botan::OID::to_formatted_string(), Botan::Exception::what(), and x509_version().
◆ v2_issuer_key_id()
| const std::vector< uint8_t > & Botan::X509_Certificate::v2_issuer_key_id | ( | ) | const |
Return the v2 issuer key ID. v2 key IDs are almost never used, instead see v3_subject_key_id.
Definition at line 370 of file x509cert.cpp.
Referenced by Botan::PKIX::check_chain().
◆ v2_subject_key_id()
| const std::vector< uint8_t > & Botan::X509_Certificate::v2_subject_key_id | ( | ) | const |
Return the v2 subject key ID. v2 key IDs are almost never used, instead see v3_subject_key_id.
Definition at line 374 of file x509cert.cpp.
Referenced by Botan::PKIX::check_chain().
◆ v3_extensions()
| const Extensions & Botan::X509_Certificate::v3_extensions | ( | ) | const |
Get all extensions of this certificate.
- Returns
- certificate extensions
Definition at line 477 of file x509cert.cpp.
Referenced by botan_x509_cert_issuer_alternative_names(), botan_x509_cert_subject_alternative_names(), Botan::PKIX::check_chain(), Botan::X509_CRL::has_matching_distribution_point(), and is_critical().
◆ verify_signature()
|
inherited |
Check the signature on this data
- Parameters
-
key the public key purportedly used to sign this data
- Returns
- status of the signature - OK if verified or otherwise an indicator of the problem preventing verification, along with the hash function that was used, for further policy checks. The second parameter is empty unless the validation was successful.
Definition at line 130 of file x509_obj.cpp.
References Botan::PK_Verifier::hash_function(), signature(), Botan::SIGNATURE_ALGO_BAD_PARAMS, Botan::SIGNATURE_ALGO_UNKNOWN, signature_algorithm(), Botan::SIGNATURE_ERROR, tbs_data(), Botan::VERIFIED, and Botan::PK_Verifier::verify_message().
Referenced by Botan::PKIX::check_chain(), and check_signature().
◆ x509_version()
| uint32_t Botan::X509_Certificate::x509_version | ( | ) | const |
Get the X509 version of this certificate object.
- Returns
- X509 version
Definition at line 350 of file x509cert.cpp.
Referenced by Botan::PKIX::check_chain(), and to_string().
The documentation for this class was generated from the following files:
- src/lib/x509/x509cert.h
- src/lib/x509/x509cert.cpp
Generated by