#include <aead.h>
Public Member Functions | |
| virtual bool | associated_data_requires_key () const |
| bool | authenticated () const |
| virtual void | clear ()=0 |
| size_t | default_nonce_length () const override |
| void | finish (secure_vector< uint8_t > &final_block, size_t offset=0) |
| template<concepts::resizable_byte_buffer T> | |
| void | finish (T &final_block, size_t offset=0) |
| virtual bool | has_keying_material () const =0 |
| virtual size_t | ideal_granularity () const =0 |
| virtual Key_Length_Specification | key_spec () const =0 |
| virtual size_t | maximum_associated_data_inputs () const |
| size_t | maximum_keylength () const |
| virtual size_t | minimum_final_size () const =0 |
| size_t | minimum_keylength () const |
| virtual std::string | name () const =0 |
| virtual size_t | output_length (size_t input_length) const =0 |
| size_t | process (std::span< uint8_t > msg) |
| size_t | process (uint8_t msg[], size_t msg_len) |
| virtual std::string | provider () const |
| virtual bool | requires_entire_message () const |
| virtual void | reset ()=0 |
| void | set_ad (std::span< const uint8_t > ad) |
| void | set_associated_data (const uint8_t ad[], size_t ad_len) |
| void | set_associated_data (std::span< const uint8_t > ad) |
| virtual void | set_associated_data_n (size_t idx, std::span< const uint8_t > ad)=0 |
| template<typename Alloc> | |
| void | set_associated_data_vec (const std::vector< uint8_t, Alloc > &ad) |
| void | set_key (const OctetString &key) |
| void | set_key (const uint8_t key[], size_t length) |
| void | set_key (std::span< const uint8_t > key) |
| void | start () |
| void | start (const uint8_t nonce[], size_t nonce_len) |
| void | start (std::span< const uint8_t > nonce) |
| virtual size_t | tag_size () const |
| template<concepts::resizable_byte_buffer T> | |
| void | update (T &buffer, size_t offset=0) |
| virtual size_t | update_granularity () const =0 |
| bool | valid_keylength (size_t length) const |
| virtual bool | valid_nonce_length (size_t nonce_len) const =0 |
Static Public Member Functions | |
| static std::unique_ptr< AEAD_Mode > | create (std::string_view algo, Cipher_Dir direction, std::string_view provider="") |
| static std::unique_ptr< AEAD_Mode > | create_or_throw (std::string_view algo, Cipher_Dir direction, std::string_view provider="") |
| static std::vector< std::string > | providers (std::string_view algo_spec) |
Protected Member Functions | |
| void | assert_key_material_set () const |
| void | assert_key_material_set (bool predicate) const |
| virtual void | finish_msg (secure_vector< uint8_t > &final_block, size_t offset=0)=0 |
| virtual size_t | process_msg (uint8_t msg[], size_t msg_len)=0 |
| virtual void | start_msg (const uint8_t nonce[], size_t nonce_len)=0 |
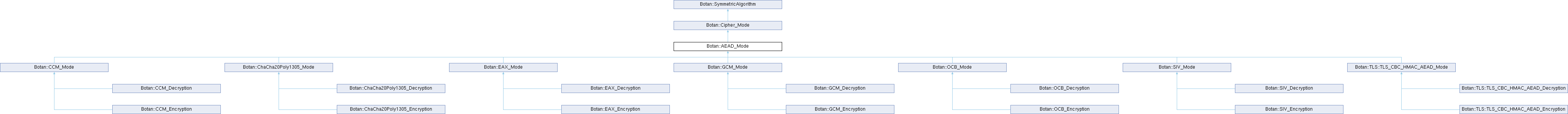
Detailed Description
Interface for AEAD (Authenticated Encryption with Associated Data) modes. These modes provide both encryption and message authentication, and can authenticate additional per-message data which is not included in the ciphertext (for instance a sequence number).
Member Function Documentation
◆ assert_key_material_set() [1/2]
|
inlineprotectedinherited |
Definition at line 145 of file sym_algo.h.
References assert_key_material_set(), and has_keying_material().
Referenced by assert_key_material_set(), Botan::Salsa20::cipher_bytes(), Botan::Lion::decrypt_n(), Botan::Lion::encrypt_n(), Botan::GHASH::final(), Botan::GHASH::nonce_hash(), Botan::GHASH::reset_associated_data(), Botan::ChaCha::seek(), Botan::CTR_BE::seek(), Botan::Salsa20::seek(), Botan::GHASH::set_associated_data(), Botan::OCB_Mode::set_associated_data_n(), Botan::Salsa20::set_iv_bytes(), Botan::GHASH::update(), and Botan::GHASH::update_associated_data().
◆ assert_key_material_set() [2/2]
|
inlineprotectedinherited |
Definition at line 147 of file sym_algo.h.
◆ associated_data_requires_key()
|
inlinevirtual |
Most AEADs require the key to be set prior to setting the AD A few allow the AD to be set even before the cipher is keyed. Such ciphers would return false from this function.
Reimplemented in Botan::Ascon_AEAD128_Mode, Botan::CCM_Mode, and Botan::ChaCha20Poly1305_Mode.
Definition at line 98 of file aead.h.
◆ authenticated()
|
inlineinherited |
Return the length in bytes of the authentication tag this algorithm generates. If the mode is not authenticated, this will return 0.
- Returns
- true iff this mode provides authentication as well as confidentiality.
Definition at line 262 of file cipher_mode.h.
References tag_size().
◆ clear()
|
pure virtualinherited |
Reset the internal state. This includes not just the key, but any partial message that may have been in process.
Implemented in Botan::AES_128, Botan::AES_192, Botan::AES_256, Botan::ANSI_X919_MAC, Botan::ARIA_128, Botan::ARIA_192, Botan::ARIA_256, Botan::Ascon_AEAD128_Mode, Botan::BLAKE2b, Botan::BLAKE2bMAC, Botan::Blowfish, Botan::Camellia_128, Botan::Camellia_192, Botan::Camellia_256, Botan::Cascade_Cipher, Botan::CAST_128, Botan::CBC_Mode, Botan::CCM_Mode, Botan::CFB_Mode, Botan::ChaCha20Poly1305_Mode, Botan::ChaCha, Botan::CMAC, Botan::CTR_BE, Botan::DES, Botan::EAX_Mode, Botan::FPE_FE1, Botan::GCM_Mode, Botan::GHASH, Botan::GMAC, Botan::GOST_28147_89, Botan::HMAC, Botan::IDEA, Botan::KMAC, Botan::Kuznyechik, Botan::Lion, Botan::Noekeon, Botan::OCB_Mode, Botan::OFB, Botan::Poly1305, Botan::RC4, Botan::Salsa20, Botan::SEED, Botan::Serpent, Botan::SHACAL2, Botan::SHAKE_Cipher, Botan::SipHash, Botan::SIV_Mode, Botan::SM4, Botan::Threefish_512, Botan::TLS::TLS_CBC_HMAC_AEAD_Mode, Botan::TLS::TLS_NULL_HMAC_AEAD_Mode, Botan::TripleDES, Botan::Twofish, and Botan::XTS_Mode.
Referenced by Botan::TLS::TLS_CBC_HMAC_AEAD_Mode::clear(), and Botan::TLS::TLS_NULL_HMAC_AEAD_Mode::clear().
◆ create()
|
static |
Create an AEAD mode
- Parameters
-
algo the algorithm to create direction specify if this should be an encryption or decryption AEAD provider optional specification for provider to use
- Returns
- an AEAD mode or a null pointer if not available
Definition at line 59 of file aead.cpp.
References Botan::SCAN_Name::algo_name(), Botan::SCAN_Name::arg(), Botan::SCAN_Name::arg_as_integer(), Botan::SCAN_Name::arg_count(), BOTAN_UNUSED, create(), Botan::BlockCipher::create(), Botan::Encryption, Botan::parse_algorithm_name(), Botan::Cipher_Mode::provider(), and Botan::split_on().
Referenced by Botan::ChaCha20Poly1305_Mode::ChaCha20Poly1305_Mode(), create(), Botan::Cipher_Mode::create(), create_or_throw(), Botan::get_aead(), and Botan::TLS::Cipher_State::is_compatible_with().
◆ create_or_throw()
|
static |
Create an AEAD mode, or throw
- Parameters
-
algo the algorithm to create direction specify if this should be an encryption or decryption AEAD provider optional specification for provider to use
- Returns
- an AEAD mode, or throw an exception
Definition at line 49 of file aead.cpp.
References create(), and Botan::Cipher_Mode::provider().
Referenced by Botan::TLS::Cipher_State::advance_with_server_hello(), Botan::TLS::Connection_Cipher_State::Connection_Cipher_State(), Botan::TLS::Session::decrypt(), and Botan::TLS::Session::encrypt().
◆ default_nonce_length()
|
inlineoverridevirtual |
- Returns
- default AEAD nonce size (a commonly supported value among AEAD modes, and large enough that random collisions are unlikely)
Implements Botan::Cipher_Mode.
Reimplemented in Botan::Ascon_AEAD128_Mode, Botan::CCM_Mode, and Botan::TLS::TLS_CBC_HMAC_AEAD_Mode.
Definition at line 130 of file aead.h.
◆ finish() [1/2]
|
inlineinherited |
Complete procession of a message with a final input of buffer, which is treated the same as with update(). If you have the entire message in hand, calling finish() without ever calling update() is both efficient and convenient.
When using an AEAD_Mode, if the supplied authentication tag does not validate, this will throw an instance of Invalid_Authentication_Tag.
If this occurs, all plaintext previously output via calls to update must be destroyed and not used in any way that an attacker could observe the effects of. This could be anything from echoing the plaintext back (perhaps in an error message), or by making an external RPC whose destination or contents depend on the plaintext. The only thing you can do is buffer it, and in the event of an invalid tag, erase the previously decrypted content from memory.
One simple way to assure this could never happen is to never call update, and instead always marshal the entire message into a single buffer and call finish on it when decrypting.
- Parameters
-
final_block in/out parameter which must be at least minimum_final_size() bytes, and will be set to any final output offset an offset into final_block to begin processing
Definition at line 178 of file cipher_mode.h.
References finish_msg().
Referenced by botan_cipher_update(), and Botan::TLS::write_record().
◆ finish() [2/2]
|
inlineinherited |
Complete procession of a message.
Note: Using this overload with anything but a Botan::secure_vector<> is copying the bytes in the in/out buffer.
- Parameters
-
final_block in/out parameter which must be at least minimum_final_size() bytes, and will be set to any final output offset an offset into final_block to begin processing
Definition at line 191 of file cipher_mode.h.
References finish_msg().
◆ finish_msg()
|
protectedpure virtualinherited |
Implemented in Botan::TLS::TLS_NULL_HMAC_AEAD_Decryption.
◆ has_keying_material()
|
pure virtualinherited |
- Returns
- true if a key has been set on this object
Implemented in Botan::AES_128, Botan::AES_192, Botan::AES_256, Botan::ANSI_X919_MAC, Botan::ARIA_128, Botan::ARIA_192, Botan::ARIA_256, Botan::Ascon_AEAD128_Mode, Botan::BLAKE2b, Botan::BLAKE2bMAC, Botan::Blowfish, Botan::Camellia_128, Botan::Camellia_192, Botan::Camellia_256, Botan::Cascade_Cipher, Botan::CAST_128, Botan::CBC_Mode, Botan::CCM_Mode, Botan::CFB_Mode, Botan::ChaCha20Poly1305_Mode, Botan::ChaCha, Botan::CMAC, Botan::CTR_BE, Botan::DES, Botan::EAX_Mode, Botan::FPE_FE1, Botan::GCM_Mode, Botan::GHASH, Botan::GMAC, Botan::GOST_28147_89, Botan::HMAC, Botan::IDEA, Botan::KMAC, Botan::Kuznyechik, Botan::Lion, Botan::Noekeon, Botan::OCB_Mode, Botan::OFB, Botan::Poly1305, Botan::RC4, Botan::Salsa20, Botan::SEED, Botan::Serpent, Botan::SHACAL2, Botan::SHAKE_Cipher, Botan::SipHash, Botan::SIV_Mode, Botan::SM4, Botan::Threefish_512, Botan::TLS::TLS_CBC_HMAC_AEAD_Mode, Botan::TLS::TLS_NULL_HMAC_AEAD_Mode, Botan::TripleDES, Botan::Twofish, and Botan::XTS_Mode.
Referenced by assert_key_material_set(), Botan::TLS::TLS_CBC_HMAC_AEAD_Mode::has_keying_material(), and Botan::TLS::TLS_NULL_HMAC_AEAD_Mode::has_keying_material().
◆ ideal_granularity()
|
pure virtualinherited |
Return an ideal granularity. This will be a multiple of the result of update_granularity but may be larger. If so it indicates that better performance may be achieved by providing buffers that are at least that size (due to SIMD execution, etc).
Implemented in Botan::Ascon_AEAD128_Mode, Botan::CBC_Mode, Botan::CCM_Mode, Botan::CFB_Mode, Botan::ChaCha20Poly1305_Mode, Botan::EAX_Mode, Botan::GCM_Mode, Botan::OCB_Mode, Botan::SIV_Mode, Botan::TLS::TLS_CBC_HMAC_AEAD_Mode, Botan::TLS::TLS_NULL_HMAC_AEAD_Mode, and Botan::XTS_Mode.
◆ key_spec()
|
pure virtualinherited |
- Returns
- object describing limits on key size
Implemented in Botan::ANSI_X919_MAC, Botan::Ascon_AEAD128_Mode, Botan::BLAKE2b, Botan::BLAKE2bMAC, Botan::Block_Cipher_Fixed_Params< BS, KMIN, KMAX, KMOD, BaseClass >, Botan::Block_Cipher_Fixed_Params< 16, 16 >, Botan::Block_Cipher_Fixed_Params< 16, 16, 32, 8 >, Botan::Block_Cipher_Fixed_Params< 16, 24 >, Botan::Block_Cipher_Fixed_Params< 16, 32 >, Botan::Block_Cipher_Fixed_Params< 32, 16, 64, 4 >, Botan::Block_Cipher_Fixed_Params< 64, 64, 0, 1, Tweakable_Block_Cipher >, Botan::Block_Cipher_Fixed_Params< 8, 1, 56 >, Botan::Block_Cipher_Fixed_Params< 8, 11, 16 >, Botan::Block_Cipher_Fixed_Params< 8, 16 >, Botan::Block_Cipher_Fixed_Params< 8, 16, 24, 8 >, Botan::Block_Cipher_Fixed_Params< 8, 32 >, Botan::Block_Cipher_Fixed_Params< 8, 8 >, Botan::Cascade_Cipher, Botan::CBC_Mode, Botan::CCM_Mode, Botan::CFB_Mode, Botan::ChaCha20Poly1305_Mode, Botan::ChaCha, Botan::CMAC, Botan::CTR_BE, Botan::EAX_Mode, Botan::FPE_FE1, Botan::GCM_Mode, Botan::GHASH, Botan::GMAC, Botan::HMAC, Botan::KMAC, Botan::Lion, Botan::OCB_Mode, Botan::OFB, Botan::Poly1305, Botan::RC4, Botan::Salsa20, Botan::SHAKE_Cipher, Botan::SipHash, Botan::SIV_Mode, Botan::TLS::TLS_CBC_HMAC_AEAD_Mode, Botan::TLS::TLS_NULL_HMAC_AEAD_Mode, and Botan::XTS_Mode.
Referenced by Botan::CBC_Mode::key_spec(), Botan::CFB_Mode::key_spec(), Botan::XTS_Mode::key_spec(), maximum_keylength(), minimum_keylength(), and valid_keylength().
◆ maximum_associated_data_inputs()
|
inlinevirtual |
Returns the maximum supported number of associated data inputs which can be provided to set_associated_data_n
If returns 0, then no associated data is supported.
Reimplemented in Botan::SIV_Mode.
Definition at line 91 of file aead.h.
◆ maximum_keylength()
|
inlineinherited |
- Returns
- maximum allowed key length
Definition at line 101 of file sym_algo.h.
References key_spec().
◆ minimum_final_size()
|
pure virtualinherited |
- Returns
- required minimum size to finalize() - may be any length larger than this.
Implemented in Botan::Ascon_AEAD128_Decryption, Botan::Ascon_AEAD128_Encryption, Botan::CBC_Decryption, Botan::CBC_Encryption, Botan::CCM_Decryption, Botan::CCM_Encryption, Botan::CFB_Mode, Botan::ChaCha20Poly1305_Decryption, Botan::ChaCha20Poly1305_Encryption, Botan::CTS_Decryption, Botan::CTS_Encryption, Botan::EAX_Decryption, Botan::EAX_Encryption, Botan::GCM_Decryption, Botan::GCM_Encryption, Botan::OCB_Decryption, Botan::OCB_Encryption, Botan::SIV_Decryption, Botan::SIV_Encryption, Botan::TLS::TLS_CBC_HMAC_AEAD_Decryption, Botan::TLS::TLS_CBC_HMAC_AEAD_Encryption, Botan::TLS::TLS_NULL_HMAC_AEAD_Decryption, Botan::TLS::TLS_NULL_HMAC_AEAD_Encryption, and Botan::XTS_Mode.
◆ minimum_keylength()
|
inlineinherited |
- Returns
- minimum allowed key length
Definition at line 106 of file sym_algo.h.
References key_spec().
◆ name()
|
pure virtualinherited |
- Returns
- the algorithm name
Implemented in Botan::AES_128, Botan::AES_192, Botan::AES_256, Botan::ANSI_X919_MAC, Botan::ARIA_128, Botan::ARIA_192, Botan::ARIA_256, Botan::Ascon_AEAD128_Mode, Botan::BLAKE2b, Botan::BLAKE2bMAC, Botan::Blowfish, Botan::Camellia_128, Botan::Camellia_192, Botan::Camellia_256, Botan::Cascade_Cipher, Botan::CAST_128, Botan::CBC_Mode, Botan::CCM_Mode, Botan::CFB_Mode, Botan::ChaCha20Poly1305_Mode, Botan::ChaCha, Botan::CMAC, Botan::CTR_BE, Botan::DES, Botan::EAX_Mode, Botan::FPE_FE1, Botan::GCM_Mode, Botan::GHASH, Botan::GMAC, Botan::GOST_28147_89, Botan::HMAC, Botan::IDEA, Botan::KMAC128, Botan::KMAC256, Botan::Kuznyechik, Botan::Lion, Botan::Noekeon, Botan::OCB_Mode, Botan::OFB, Botan::Poly1305, Botan::RC4, Botan::Salsa20, Botan::SEED, Botan::Serpent, Botan::SHACAL2, Botan::SHAKE_128_Cipher, Botan::SHAKE_256_Cipher, Botan::SipHash, Botan::SIV_Mode, Botan::SM4, Botan::Threefish_512, Botan::TLS::TLS_CBC_HMAC_AEAD_Mode, Botan::TLS::TLS_NULL_HMAC_AEAD_Mode, Botan::TripleDES, Botan::Twofish, and Botan::XTS_Mode.
Referenced by Botan::XTS_Mode::name(), set_key(), and Botan::MessageAuthenticationCode::start_msg().
◆ output_length()
|
pure virtualinherited |
Returns the size of the output if this transform is used to process a message with input_length bytes. In most cases the answer is precise. If it is not possible to precise (namely for CBC decryption) instead an upper bound is returned.
Implemented in Botan::Ascon_AEAD128_Decryption, Botan::Ascon_AEAD128_Encryption, Botan::CBC_Decryption, Botan::CBC_Encryption, Botan::CCM_Decryption, Botan::CCM_Encryption, Botan::CFB_Mode, Botan::ChaCha20Poly1305_Decryption, Botan::ChaCha20Poly1305_Encryption, Botan::CTS_Encryption, Botan::EAX_Decryption, Botan::EAX_Encryption, Botan::GCM_Decryption, Botan::GCM_Encryption, Botan::OCB_Decryption, Botan::OCB_Encryption, Botan::SIV_Decryption, Botan::SIV_Encryption, Botan::TLS::TLS_CBC_HMAC_AEAD_Decryption, Botan::TLS::TLS_CBC_HMAC_AEAD_Encryption, Botan::TLS::TLS_NULL_HMAC_AEAD_Decryption, Botan::TLS::TLS_NULL_HMAC_AEAD_Encryption, Botan::XTS_Decryption, and Botan::XTS_Encryption.
Referenced by Botan::TLS::TLS_CBC_HMAC_AEAD_Mode::TLS_CBC_HMAC_AEAD_Mode(), Botan::TLS::TLS_NULL_HMAC_AEAD_Mode::TLS_NULL_HMAC_AEAD_Mode(), and Botan::TLS::write_record().
◆ process() [1/2]
|
inlineinherited |
Process message blocks
Input must be a multiple of update_granularity
Processes msg in place and returns bytes written. Normally this will be either msg_len (indicating the entire message was processed) or for certain AEAD modes zero (indicating that the mode requires the entire message be processed in one pass).
- Parameters
-
msg the message to be processed
- Returns
- bytes written in-place
Definition at line 131 of file cipher_mode.h.
References process_msg().
Referenced by botan_cipher_update(), Botan::TLS::TLS_NULL_HMAC_AEAD_Decryption::finish_msg(), and update().
◆ process() [2/2]
|
inlineinherited |
◆ process_msg()
|
protectedpure virtualinherited |
◆ provider()
|
inlinevirtualinherited |
- Returns
- provider information about this implementation. Default is "base", might also return "sse2", "avx2", "openssl", or some other arbitrary string.
Reimplemented in Botan::GCM_Mode.
Definition at line 273 of file cipher_mode.h.
Referenced by Botan::AEAD_Mode::create(), create(), Botan::AEAD_Mode::create_or_throw(), and create_or_throw().
◆ providers()
|
staticinherited |
- Returns
- list of available providers for this algorithm, empty if not available
- Parameters
-
algo_spec algorithm name
Definition at line 171 of file cipher_mode.cpp.
References create(), Botan::Encryption, and providers().
Referenced by providers().
◆ requires_entire_message()
|
inlinevirtualinherited |
Certain modes require the entire message be available before any processing can occur. For such modes, input will be consumed but not returned, until finish is called, which returns the entire message.
This function returns true if this mode has this style of operation.
Reimplemented in Botan::CCM_Mode, and Botan::SIV_Mode.
Definition at line 232 of file cipher_mode.h.
Referenced by botan_cipher_update().
◆ reset()
|
pure virtualinherited |
Resets just the message specific state and allows encrypting again under the existing key
Implemented in Botan::Ascon_AEAD128_Mode, Botan::CBC_Decryption, Botan::CBC_Mode, Botan::CCM_Mode, Botan::CFB_Mode, Botan::ChaCha20Poly1305_Mode, Botan::EAX_Mode, Botan::GCM_Mode, Botan::OCB_Mode, Botan::SIV_Mode, Botan::TLS::TLS_CBC_HMAC_AEAD_Mode, Botan::TLS::TLS_NULL_HMAC_AEAD_Mode, and Botan::XTS_Mode.
◆ set_ad()
|
inline |
Set associated data that is not included in the ciphertext but that should be authenticated. Must be called after set_key() and before start().
- Parameters
-
ad the associated data
Definition at line 124 of file aead.h.
References set_ad(), and set_associated_data().
Referenced by set_ad().
◆ set_associated_data() [1/2]
|
inline |
Definition at line 61 of file aead.h.
References set_associated_data().
Referenced by set_associated_data().
◆ set_associated_data() [2/2]
|
inline |
Set associated data that is not included in the ciphertext but that should be authenticated. Must be called after set_key() and before start().
Unless reset by another call, the associated data is kept between messages. Thus, if the AD does not change, calling once (after set_key()) is the optimum.
- Parameters
-
ad the associated data
Definition at line 59 of file aead.h.
References set_associated_data_n().
Referenced by set_ad(), set_associated_data_vec(), and Botan::TLS::write_record().
◆ set_associated_data_n()
|
pure virtual |
Set associated data that is not included in the ciphertext but that should be authenticated. Must be called after set_key() and before start().
Unless reset by another call, the associated data is kept between messages. Thus, if the AD does not change, calling once (after set_key()) is the optimum.
Some AEADs (namely SIV) support multiple AD inputs. For all other modes only nominal AD input 0 is supported; all other values of idx will cause an exception.
Derived AEADs must implement this. For AEADs where maximum_associated_data_inputs() returns 1 (the default), the idx must simply be ignored.
- Parameters
-
idx which associated data to set ad the associated data
Implemented in Botan::Ascon_AEAD128_Mode, Botan::CCM_Mode, Botan::ChaCha20Poly1305_Mode, Botan::EAX_Mode, Botan::GCM_Mode, Botan::OCB_Mode, Botan::SIV_Mode, Botan::TLS::TLS_CBC_HMAC_AEAD_Encryption, Botan::TLS::TLS_CBC_HMAC_AEAD_Mode, Botan::TLS::TLS_NULL_HMAC_AEAD_Encryption, and Botan::TLS::TLS_NULL_HMAC_AEAD_Mode.
Referenced by set_associated_data().
◆ set_associated_data_vec()
|
inline |
Set associated data that is not included in the ciphertext but that should be authenticated. Must be called after set_key() and before start().
- Parameters
-
ad the associated data
Definition at line 111 of file aead.h.
References set_associated_data(), and set_associated_data_vec().
Referenced by set_associated_data_vec().
◆ set_key() [1/3]
|
inherited |
Set the symmetric key of this object.
- Parameters
-
key the SymmetricKey to be set.
Definition at line 14 of file sym_algo.cpp.
References Botan::OctetString::begin(), Botan::OctetString::length(), and set_key().
Referenced by Botan::create_aes_row_generator(), Botan::Sodium::crypto_stream_salsa20(), Botan::Sodium::crypto_stream_salsa20_xor_ic(), Botan::Sodium::crypto_stream_xsalsa20(), Botan::Sodium::crypto_stream_xsalsa20_xor_ic(), Botan::FPE::fe1_decrypt(), Botan::FPE::fe1_encrypt(), Botan::Sphincs_Hash_Functions_Sha2::PRF_msg(), Botan::Sodium::randombytes_buf_deterministic(), Botan::TLS::TLS_NULL_HMAC_AEAD_Mode::reset(), and set_key().
◆ set_key() [2/3]
|
inlineinherited |
Set the symmetric key of this object.
- Parameters
-
key the to be set as a byte array. length in bytes of key param
Definition at line 132 of file sym_algo.h.
References set_key().
Referenced by set_key().
◆ set_key() [3/3]
|
inherited |
Set the symmetric key of this object.
- Parameters
-
key the contiguous byte range to be set.
Definition at line 22 of file sym_algo.cpp.
References name(), and valid_keylength().
◆ start() [1/3]
|
inlineinherited |
Begin processing a message.
The exact semantics of this depend on the mode. For many modes, the call will fail since a nonce must be provided.
For certain modes such as CBC this will instead cause the last ciphertext block to be used as the nonce of the new message; doing this isn't a good idea, but some (mostly older) protocols do this.
Definition at line 116 of file cipher_mode.h.
References start_msg().
◆ start() [2/3]
|
inlineinherited |
Begin processing a message with a fresh nonce.
- Parameters
-
nonce the per message nonce nonce_len length of nonce
Definition at line 104 of file cipher_mode.h.
References start_msg().
◆ start() [3/3]
|
inlineinherited |
Begin processing a message with a fresh nonce.
- Warning
- Typically one must not reuse the same nonce for more than one message under the same key. For most cipher modes this would mean total loss of security and/or authenticity guarantees.
- Note
- If reliably generating unique nonces is difficult in your environment, use SIV which retains security even if nonces are repeated.
- Parameters
-
nonce the per message nonce
Definition at line 97 of file cipher_mode.h.
References start_msg().
Referenced by botan_cipher_start(), and Botan::TLS::write_record().
◆ start_msg()
|
protectedpure virtualinherited |
Implemented in Botan::Ascon_AEAD128_Mode.
◆ tag_size()
|
inlinevirtualinherited |
- Returns
- the size of the authentication tag used (in bytes)
Reimplemented in Botan::Ascon_AEAD128_Mode, Botan::CCM_Mode, Botan::ChaCha20Poly1305_Mode, Botan::EAX_Mode, Botan::GCM_Mode, Botan::OCB_Mode, Botan::SIV_Mode, Botan::TLS::TLS_CBC_HMAC_AEAD_Mode, and Botan::TLS::TLS_NULL_HMAC_AEAD_Mode.
Definition at line 267 of file cipher_mode.h.
Referenced by authenticated().
◆ update()
|
inlineinherited |
Process some data. Input must be in size update_granularity() uint8_t blocks. The buffer is an in/out parameter and may be resized. In particular, some modes require that all input be consumed before any output is produced; with these modes, buffer will be returned empty.
The first offset bytes of buffer will be ignored (this allows in place processing of a buffer that contains an initial plaintext header).
- Parameters
-
buffer in/out parameter which will possibly be resized offset an offset into blocks to begin processing
Definition at line 148 of file cipher_mode.h.
References process().
◆ update_granularity()
|
pure virtualinherited |
The :cpp:class:Cipher_Mode interface requires message processing in multiples of the block size. This returns size of required blocks to update. If the mode implementation does not require buffering it will return 1.
- Returns
- size of required blocks to update
Implemented in Botan::Ascon_AEAD128_Mode, Botan::CBC_Mode, Botan::CCM_Mode, Botan::CFB_Mode, Botan::ChaCha20Poly1305_Mode, Botan::EAX_Mode, Botan::GCM_Mode, Botan::OCB_Mode, Botan::SIV_Mode, Botan::TLS::TLS_CBC_HMAC_AEAD_Mode, Botan::TLS::TLS_NULL_HMAC_AEAD_Mode, and Botan::XTS_Mode.
◆ valid_keylength()
|
inlineinherited |
Check whether a given key length is valid for this algorithm.
- Parameters
-
length the key length to be checked.
- Returns
- true if the key length is valid.
Definition at line 113 of file sym_algo.h.
References key_spec().
Referenced by set_key().
◆ valid_nonce_length()
|
pure virtualinherited |
- Returns
- true iff nonce_len is a valid length for the nonce
Implemented in Botan::Ascon_AEAD128_Mode, Botan::CBC_Mode, Botan::CCM_Mode, Botan::CFB_Mode, Botan::ChaCha20Poly1305_Mode, Botan::CTS_Decryption, Botan::CTS_Encryption, Botan::EAX_Mode, Botan::GCM_Mode, Botan::OCB_Mode, Botan::SIV_Mode, Botan::TLS::TLS_CBC_HMAC_AEAD_Mode, Botan::TLS::TLS_NULL_HMAC_AEAD_Mode, and Botan::XTS_Mode.
The documentation for this class was generated from the following files:
Generated by