#include <chacha_rng.h>
Public Member Functions | |
| bool | accepts_input () const final |
| void | add_entropy (const uint8_t input[], size_t length) |
| void | add_entropy (std::span< const uint8_t > input) |
| template<typename T> | |
| void | add_entropy_T (const T &t) |
| ChaCha_RNG () | |
| BOTAN_FUTURE_EXPLICIT | ChaCha_RNG (Entropy_Sources &entropy_sources, size_t reseed_interval=RandomNumberGenerator::DefaultReseedInterval) |
| ChaCha_RNG (RandomNumberGenerator &underlying_rng, Entropy_Sources &entropy_sources, size_t reseed_interval=RandomNumberGenerator::DefaultReseedInterval) | |
| BOTAN_FUTURE_EXPLICIT | ChaCha_RNG (RandomNumberGenerator &underlying_rng, size_t reseed_interval=RandomNumberGenerator::DefaultReseedInterval) |
| BOTAN_FUTURE_EXPLICIT | ChaCha_RNG (std::span< const uint8_t > seed) |
| void | clear () final |
| void | force_reseed () |
| void | initialize_with (const uint8_t input[], size_t length) |
| void | initialize_with (std::span< const uint8_t > input) |
| bool | is_seeded () const final |
| size_t | max_number_of_bytes_per_request () const override |
| std::string | name () const override |
| uint8_t | next_byte () |
| uint8_t | next_nonzero_byte () |
| template<size_t bytes> | |
| std::array< uint8_t, bytes > | random_array () |
| template<concepts::resizable_byte_buffer T = secure_vector<uint8_t>> | |
| T | random_vec (size_t bytes) |
| void | random_vec (std::span< uint8_t > v) |
| template<concepts::resizable_byte_buffer T> | |
| void | random_vec (T &v, size_t bytes) |
| void | randomize (std::span< uint8_t > output) |
| void | randomize (uint8_t output[], size_t length) |
| void | randomize_with_input (std::span< uint8_t > output, std::span< const uint8_t > input) |
| void | randomize_with_input (uint8_t output[], size_t output_len, const uint8_t input[], size_t input_len) |
| void | randomize_with_ts_input (std::span< uint8_t > output) |
| void | randomize_with_ts_input (uint8_t output[], size_t output_len) |
| size_t | reseed (Entropy_Sources &srcs, size_t poll_bits=RandomNumberGenerator::DefaultPollBits, std::chrono::milliseconds=DefaultPollTimeout) |
| size_t | reseed_from (Entropy_Sources &srcs, size_t poll_bits=RandomNumberGenerator::DefaultPollBits) |
| void | reseed_from (RandomNumberGenerator &rng, size_t poll_bits=RandomNumberGenerator::DefaultPollBits) |
| void | reseed_from_rng (RandomNumberGenerator &rng, size_t poll_bits=RandomNumberGenerator::DefaultPollBits) final |
| size_t | reseed_from_sources (Entropy_Sources &srcs, size_t poll_bits=RandomNumberGenerator::DefaultPollBits) final |
| size_t | reseed_interval () const |
| size_t | security_level () const override |
Static Public Attributes | |
| static constexpr size_t | DefaultPollBits = 256 |
| static constexpr auto | DefaultPollTimeout = std::chrono::milliseconds(50) |
| static constexpr size_t | DefaultReseedInterval = 1024 |
Protected Member Functions | |
| void | reseed_check () |
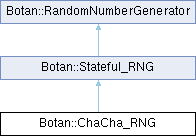
Detailed Description
ChaCha_RNG is a very fast but completely ad-hoc RNG created by creating a 256-bit random value and using it as a key for ChaCha20.
The RNG maintains two 256-bit keys, one for HMAC_SHA256 (HK) and the other for ChaCha20 (CK). To compute a new key in response to reseeding request or add_entropy calls, ChaCha_RNG computes CK' = HMAC_SHA256(HK, input_material) Then a new HK' is computed by running ChaCha20 with the new key to output 32 bytes: HK' = ChaCha20(CK')
Now output can be produced by continuing to produce output with ChaCha20 under CK'
The first HK (before seeding occurs) is taken as the all zero value.
- Warning
- This RNG construction is probably fine but is non-standard. The primary reason to use it is in cases where the other RNGs are not fast enough.
Definition at line 40 of file chacha_rng.h.
Constructor & Destructor Documentation
◆ ChaCha_RNG() [1/5]
| Botan::ChaCha_RNG::ChaCha_RNG | ( | ) |
Automatic reseeding is disabled completely, as it has no access to any source for seed material.
If a fork is detected, the RNG will be unable to reseed itself in response. In this case, an exception will be thrown rather than generating duplicated output.
Definition at line 14 of file chacha_rng.cpp.
References Botan::Stateful_RNG::clear(), Botan::MessageAuthenticationCode::create_or_throw(), and Botan::StreamCipher::create_or_throw().
◆ ChaCha_RNG() [2/5]
| Botan::ChaCha_RNG::ChaCha_RNG | ( | std::span< const uint8_t > | seed | ) |
Provide an initial seed to the RNG, without providing an underlying RNG or entropy source. Automatic reseeding is disabled completely, as it has no access to any source for seed material.
If a fork is detected, the RNG will be unable to reseed itself in response. In this case, an exception will be thrown rather than generating duplicated output.
- Parameters
-
SEED the seed material, should be at least 256 bits
Definition at line 20 of file chacha_rng.cpp.
References Botan::RandomNumberGenerator::add_entropy(), Botan::Stateful_RNG::clear(), Botan::MessageAuthenticationCode::create_or_throw(), and Botan::StreamCipher::create_or_throw().
◆ ChaCha_RNG() [3/5]
| Botan::ChaCha_RNG::ChaCha_RNG | ( | RandomNumberGenerator & | underlying_rng, |
| size_t | reseed_interval = RandomNumberGenerator::DefaultReseedInterval ) |
Automatic reseeding from underlying_rng will take place after reseed_interval many requests or after a fork was detected.
- Parameters
-
underlying_rng is a reference to some RNG which will be used to perform the periodic reseeding reseed_interval specifies a limit of how many times the RNG will be called before automatic reseeding is performed
Definition at line 27 of file chacha_rng.cpp.
References Botan::Stateful_RNG::clear(), Botan::MessageAuthenticationCode::create_or_throw(), Botan::StreamCipher::create_or_throw(), Botan::Stateful_RNG::reseed_interval(), and Botan::Stateful_RNG::Stateful_RNG().
◆ ChaCha_RNG() [4/5]
| Botan::ChaCha_RNG::ChaCha_RNG | ( | Entropy_Sources & | entropy_sources, |
| size_t | reseed_interval = RandomNumberGenerator::DefaultReseedInterval ) |
Automatic reseeding from entropy_sources will take place after reseed_interval many requests or after a fork was detected.
- Parameters
-
entropy_sources will be polled to perform reseeding periodically reseed_interval specifies a limit of how many times the RNG will be called before automatic reseeding is performed.
Definition at line 43 of file chacha_rng.cpp.
References Botan::Stateful_RNG::clear(), Botan::MessageAuthenticationCode::create_or_throw(), Botan::StreamCipher::create_or_throw(), Botan::Stateful_RNG::reseed_interval(), and Botan::Stateful_RNG::Stateful_RNG().
◆ ChaCha_RNG() [5/5]
| Botan::ChaCha_RNG::ChaCha_RNG | ( | RandomNumberGenerator & | underlying_rng, |
| Entropy_Sources & | entropy_sources, | ||
| size_t | reseed_interval = RandomNumberGenerator::DefaultReseedInterval ) |
Automatic reseeding from underlying_rng and entropy_sources will take place after reseed_interval many requests or after a fork was detected.
- Parameters
-
underlying_rng is a reference to some RNG which will be used to perform the periodic reseeding entropy_sources will be polled to perform reseeding periodically reseed_interval specifies a limit of how many times the RNG will be called before automatic reseeding is performed.
Definition at line 34 of file chacha_rng.cpp.
References Botan::Stateful_RNG::clear(), Botan::MessageAuthenticationCode::create_or_throw(), Botan::StreamCipher::create_or_throw(), Botan::Stateful_RNG::reseed_interval(), and Botan::Stateful_RNG::Stateful_RNG().
Member Function Documentation
◆ accepts_input()
|
inlinefinalvirtualinherited |
Returns false if it is known that this RNG object is not able to accept externally provided inputs (via add_entropy, randomize_with_input, etc). In this case, any such provided inputs are ignored.
If this function returns true, then inputs may or may not be accepted.
Implements Botan::RandomNumberGenerator.
Definition at line 71 of file stateful_rng.h.
References accepts_input().
Referenced by accepts_input().
◆ add_entropy() [1/2]
|
inlineinherited |
Definition at line 100 of file rng.h.
References add_entropy().
Referenced by add_entropy().
◆ add_entropy() [2/2]
|
inlineinherited |
Incorporate some additional data into the RNG state. For example adding nonces or timestamps from a peer's protocol message can help hedge against VM state rollback attacks. A few RNG types do not accept any externally provided input, in which case this function is a no-op.
- Parameters
-
input a byte array containing the entropy to be added
Definition at line 98 of file rng.h.
References fill_bytes_with_input().
Referenced by add_entropy_T(), Botan::ChaCha_RNG::ChaCha_RNG(), Botan::Stateful_RNG::initialize_with(), Botan::Getentropy::poll(), Botan::Intel_Rdseed::poll(), and reseed_from_rng().
◆ add_entropy_T()
|
inlineinherited |
Incorporate some additional data into the RNG state.
Definition at line 107 of file rng.h.
References add_entropy().
Referenced by Botan::Win32_EntropySource::poll().
◆ clear()
|
finalvirtualinherited |
Clear all internally held values of this RNG
- Postcondition
- is_seeded() == false if the RNG has an internal state that can be cleared.
Implements Botan::RandomNumberGenerator.
Definition at line 15 of file stateful_rng.cpp.
References clear_state(), and Botan::lock().
Referenced by Botan::ChaCha_RNG::ChaCha_RNG(), Botan::ChaCha_RNG::ChaCha_RNG(), Botan::ChaCha_RNG::ChaCha_RNG(), Botan::ChaCha_RNG::ChaCha_RNG(), Botan::ChaCha_RNG::ChaCha_RNG(), Botan::HMAC_DRBG::HMAC_DRBG(), Botan::HMAC_DRBG::HMAC_DRBG(), Botan::HMAC_DRBG::HMAC_DRBG(), Botan::HMAC_DRBG::HMAC_DRBG(), Botan::HMAC_DRBG::HMAC_DRBG(), and initialize_with().
◆ force_reseed()
|
inherited |
Mark state as requiring a reseed on next use
Definition at line 22 of file stateful_rng.cpp.
References Botan::lock().
◆ initialize_with() [1/2]
|
inlineinherited |
Definition at line 67 of file stateful_rng.h.
References initialize_with().
Referenced by initialize_with().
◆ initialize_with() [2/2]
|
inherited |
Consume this input and mark the RNG as initialized regardless of the length of the input or the current seeded state of the RNG.
Definition at line 32 of file stateful_rng.cpp.
References Botan::RandomNumberGenerator::add_entropy(), clear(), and Botan::lock().
◆ is_seeded()
|
finalvirtualinherited |
Check whether this RNG is seeded.
- Returns
- true if this RNG was already seeded, false otherwise.
Implements Botan::RandomNumberGenerator.
Definition at line 27 of file stateful_rng.cpp.
References Botan::lock().
Referenced by reseed_check().
◆ max_number_of_bytes_per_request()
|
inlineoverridevirtual |
Some DRBGs have a notion of the maximum number of bytes per request. Longer requests (to randomize) will be treated as multiple requests, and may initiate reseeding multiple times, depending on the values of max_number_of_bytes_per_request and reseed_interval(). This function returns zero if the RNG in question does not have such a notion.
- Returns
- max number of bytes per request (or zero)
Implements Botan::Stateful_RNG.
Definition at line 108 of file chacha_rng.h.
◆ name()
|
inlineoverridevirtual |
- Returns
- the name of this RNG type
Implements Botan::RandomNumberGenerator.
Definition at line 104 of file chacha_rng.h.
◆ next_byte()
|
inlineinherited |
Return a random byte
- Returns
- random byte
- Exceptions
-
PRNG_Unseeded if the RNG fails because it has not enough entropy Exception if the RNG fails
Definition at line 252 of file rng.h.
References fill_bytes_with_input().
Referenced by next_nonzero_byte(), and Botan::random_prime().
◆ next_nonzero_byte()
|
inlineinherited |
- Returns
- a random byte that is greater than zero
- Exceptions
-
PRNG_Unseeded if the RNG fails because it has not enough entropy Exception if the RNG fails
Definition at line 263 of file rng.h.
References next_byte().
◆ random_array()
|
inlineinherited |
Create a std::array of bytes random bytes
Definition at line 240 of file rng.h.
References random_vec().
◆ random_vec() [1/3]
|
inlineinherited |
Create some byte container type and fill it with some random bytes.
- Template Parameters
-
T the desired byte container type (e.g std::vector<uint8_t>)
- Parameters
-
bytes number of random bytes to initialize the container with
- Returns
- a container of type T with
bytesrandom bytes
Definition at line 230 of file rng.h.
References random_vec().
◆ random_vec() [2/3]
|
inlineinherited |
Fill a given byte container with bytes random bytes
- Todo
- deprecate this overload (in favor of randomize())
- Parameters
-
v the container to be filled with bytesrandom bytes
Definition at line 204 of file rng.h.
References randomize().
Referenced by Botan::Classic_McEliece_PrivateKey::Classic_McEliece_PrivateKey(), Botan::TLS::Client_Key_Exchange::Client_Key_Exchange(), Botan::TLS::Client_Key_Exchange::Client_Key_Exchange(), Botan::PK_Decryptor::decrypt_or_random(), Botan::Dilithium_PrivateKey::Dilithium_PrivateKey(), Botan::Ed25519_PrivateKey::Ed25519_PrivateKey(), Botan::Kyber_KEM_Encryptor::encapsulate(), Botan::ML_KEM_Encryptor::encapsulate(), Botan::TLS::Session::encrypt(), Botan::KeyPair::encryption_consistency_check(), Botan::FrodoKEM_PrivateKey::FrodoKEM_PrivateKey(), Botan::generate_bcrypt(), Botan::Kyber_PrivateKey::Kyber_PrivateKey(), Botan::TLS::make_hello_random(), Botan::OctetString::OctetString(), random_array(), random_vec(), random_vec(), Botan::BigInt::randomize(), reseed_from_rng(), Botan::SphincsPlus_PrivateKey::SphincsPlus_PrivateKey(), Botan::X25519_PrivateKey::X25519_PrivateKey(), and Botan::XMSS_PublicKey::XMSS_PublicKey().
◆ random_vec() [3/3]
|
inlineinherited |
Resize a given byte container to bytes and fill it with random bytes
- Template Parameters
-
T the desired byte container type (e.g std::vector<uint8_t>)
- Parameters
-
v the container to be filled with bytesrandom bytesbytes number of random bytes to initialize the container with
Definition at line 215 of file rng.h.
References random_vec().
◆ randomize() [1/2]
|
inlineinherited |
Randomize a byte array.
May block shortly if e.g. the RNG is not yet initialized or a retry because of insufficient entropy is needed.
- Parameters
-
output the byte array to hold the random output.
- Exceptions
-
PRNG_Unseeded if the RNG fails because it has not enough entropy Exception if the RNG fails
Definition at line 75 of file rng.h.
References fill_bytes_with_input().
Referenced by Botan::TLS::Connection_Cipher_State::aead_nonce(), Botan::argon2_generate_pwhash(), Botan::BlindedScalarBits< C, WindowBits+1 >::BlindedScalarBits(), botan_system_rng_get(), Botan::CryptoBox::encrypt(), Botan::generate_dsa_primes(), Botan::generate_passhash9(), Botan::IntMod< MontgomeryRep< ScalarParams > >::random(), Botan::random_gf2m(), Botan::McEliece_PublicKey::random_plaintext_element(), Botan::random_prime(), random_vec(), Botan::Sodium::randombytes_buf(), randomize_with_ts_input(), Botan::KeyPair::signature_consistency_check(), Botan::RTSS_Share::split(), and Botan::UUID::UUID().
◆ randomize() [2/2]
|
inlineinherited |
Definition at line 77 of file rng.h.
References randomize().
Referenced by randomize().
◆ randomize_with_input() [1/2]
|
inlineinherited |
Incorporate entropy into the RNG state then produce output. Some RNG types implement this using a single operation, default calls add_entropy + randomize in sequence.
Use this to further bind the outputs to your current process/protocol state. For instance if generating a new key for use in a session, include a session ID or other such value. See NIST SP 800-90 A, B, C series for more ideas.
- Parameters
-
output buffer to hold the random output input entropy buffer to incorporate
- Exceptions
-
PRNG_Unseeded if the RNG fails because it has not enough entropy Exception if the RNG fails Exception may throw if the RNG accepts input, but adding the entropy failed.
Definition at line 127 of file rng.h.
References fill_bytes_with_input().
Referenced by Botan::System_RNG::fill_bytes_with_input(), and randomize_with_input().
◆ randomize_with_input() [2/2]
|
inlineinherited |
Definition at line 131 of file rng.h.
References randomize_with_input().
◆ randomize_with_ts_input() [1/2]
|
inherited |
This calls randomize_with_input using some timestamps as extra input.
For a stateful RNG using non-random but potentially unique data the extra input can help protect against problems with fork, VM state rollback, or other cases where somehow an RNG state is duplicated. If both of the duplicated RNG states later incorporate a timestamp (and the timestamps don't themselves repeat), their outputs will diverge.
- Parameters
-
output buffer to hold the random output
- Exceptions
-
PRNG_Unseeded if the RNG fails because it has not enough entropy Exception if the RNG fails Exception may throw if the RNG accepts input, but adding the entropy failed.
Definition at line 28 of file rng.cpp.
References accepts_input(), BOTAN_UNUSED, fill_bytes_with_input(), Botan::OS::get_high_resolution_clock(), Botan::OS::get_process_id(), randomize(), Botan::store_le(), and Botan::system_rng().
Referenced by randomize_with_ts_input().
◆ randomize_with_ts_input() [2/2]
|
inlineinherited |
Definition at line 151 of file rng.h.
References randomize_with_ts_input().
◆ reseed()
|
inlineinherited |
Poll provided sources for up to poll_bits bits of entropy. Returns estimate of the number of bits collected.
Sets the seeded state to true if enough entropy was added.
TODO(Botan4) remove this function
Definition at line 296 of file rng.h.
References DefaultPollBits, DefaultPollTimeout, RandomNumberGenerator(), reseed(), and reseed_from().
Referenced by reseed().
◆ reseed_check()
|
protectedinherited |
Definition at line 105 of file stateful_rng.cpp.
References BOTAN_ASSERT, Botan::OS::get_process_id(), is_seeded(), Botan::RandomNumberGenerator::name(), reseed_from_rng(), reseed_from_sources(), and security_level().
◆ reseed_from() [1/2]
|
inlineinherited |
Poll provided sources for up to poll_bits bits of entropy. Returns estimate of the number of bits collected. Sets the seeded state to true if enough entropy was added.
Definition at line 179 of file rng.h.
References DefaultPollBits, and reseed_from_sources().
Referenced by reseed().
◆ reseed_from() [2/2]
|
inlineinherited |
Reseed by reading specified bits from the RNG
Sets the seeded state to true if enough entropy was added.
Definition at line 190 of file rng.h.
References DefaultPollBits, RandomNumberGenerator(), and reseed_from_rng().
◆ reseed_from_rng()
|
finalvirtualinherited |
Reseed by reading specified bits from the RNG
Sets the seeded state to true if enough entropy was added.
Reimplemented from Botan::RandomNumberGenerator.
Definition at line 90 of file stateful_rng.cpp.
References Botan::lock(), Botan::RandomNumberGenerator::RandomNumberGenerator(), Botan::RandomNumberGenerator::reseed_from_rng(), and security_level().
Referenced by reseed_check().
◆ reseed_from_sources()
|
finalvirtualinherited |
Poll provided sources for up to poll_bits bits of entropy. Returns estimate of the number of bits collected.
Reimplemented from Botan::RandomNumberGenerator.
Definition at line 78 of file stateful_rng.cpp.
References Botan::lock(), Botan::RandomNumberGenerator::reseed_from_sources(), and security_level().
Referenced by reseed_check().
◆ reseed_interval()
|
inlineinherited |
Definition at line 104 of file stateful_rng.h.
Referenced by Botan::ChaCha_RNG::ChaCha_RNG(), Botan::ChaCha_RNG::ChaCha_RNG(), Botan::ChaCha_RNG::ChaCha_RNG(), Botan::HMAC_DRBG::HMAC_DRBG(), Botan::HMAC_DRBG::HMAC_DRBG(), Botan::HMAC_DRBG::HMAC_DRBG(), Stateful_RNG(), Stateful_RNG(), and Stateful_RNG().
◆ security_level()
|
overridevirtual |
- Returns
- intended security level of this DRBG
Implements Botan::Stateful_RNG.
Definition at line 72 of file chacha_rng.cpp.
Member Data Documentation
◆ DefaultPollBits
|
staticconstexprinherited |
Number of entropy bits polled for reseeding userspace RNGs like HMAC_DRBG
Definition at line 50 of file rng.h.
Referenced by reseed(), reseed_from(), and reseed_from().
◆ DefaultPollTimeout
|
staticconstexprinherited |
◆ DefaultReseedInterval
|
staticconstexprinherited |
The documentation for this class was generated from the following files:
- src/lib/rng/chacha_rng/chacha_rng.h
- src/lib/rng/chacha_rng/chacha_rng.cpp
Generated by