#include <kdf.h>
Public Member Functions | |
| KDF * | clone () const |
| template<concepts::resizable_byte_buffer T = secure_vector<uint8_t>> | |
| T | derive_key (size_t key_len, const uint8_t secret[], size_t secret_len, const uint8_t salt[], size_t salt_len, const uint8_t label[]=nullptr, size_t label_len=0) const |
| template<concepts::resizable_byte_buffer T = secure_vector<uint8_t>> | |
| T | derive_key (size_t key_len, const uint8_t secret[], size_t secret_len, std::string_view salt="", std::string_view label="") const |
| template<concepts::resizable_byte_buffer T = secure_vector<uint8_t>> | |
| T | derive_key (size_t key_len, std::span< const uint8_t > secret, const uint8_t salt[], size_t salt_len, std::string_view label="") const |
| template<concepts::resizable_byte_buffer T = secure_vector<uint8_t>> | |
| T | derive_key (size_t key_len, std::span< const uint8_t > secret, std::span< const uint8_t > salt, std::span< const uint8_t > label) const |
| template<concepts::resizable_byte_buffer T = secure_vector<uint8_t>> | |
| T | derive_key (size_t key_len, std::span< const uint8_t > secret, std::string_view salt="", std::string_view label="") const |
| template<size_t key_len> | |
| std::array< uint8_t, key_len > | derive_key (std::span< const uint8_t > secret, std::span< const uint8_t > salt={}, std::span< const uint8_t > label={}) |
| template<size_t key_len> | |
| std::array< uint8_t, key_len > | derive_key (std::span< const uint8_t > secret, std::span< const uint8_t > salt={}, std::string_view label="") |
| template<size_t key_len> | |
| std::array< uint8_t, key_len > | derive_key (std::span< const uint8_t > secret, std::string_view salt="", std::string_view label="") |
| void | derive_key (std::span< uint8_t > key, std::span< const uint8_t > secret, std::span< const uint8_t > salt, std::span< const uint8_t > label) const |
| void | kdf (uint8_t key[], size_t key_len, const uint8_t secret[], size_t secret_len, const uint8_t salt[], size_t salt_len, const uint8_t label[], size_t label_len) const |
| virtual std::string | name () const =0 |
| virtual std::unique_ptr< KDF > | new_object () const =0 |
| virtual | ~KDF ()=default |
Static Public Member Functions | |
| static std::unique_ptr< KDF > | create (std::string_view algo_spec, std::string_view provider="") |
| static std::unique_ptr< KDF > | create_or_throw (std::string_view algo_spec, std::string_view provider="") |
| static std::vector< std::string > | providers (std::string_view algo_spec) |
Protected Member Functions | |
| virtual void | perform_kdf (std::span< uint8_t > key, std::span< const uint8_t > secret, std::span< const uint8_t > salt, std::span< const uint8_t > label) const =0 |
Detailed Description
Constructor & Destructor Documentation
◆ ~KDF()
|
virtualdefault |
References create(), create_or_throw(), and providers().
Member Function Documentation
◆ clone()
|
inline |
- Returns
- new object representing the same algorithm as *this
Definition at line 242 of file kdf.h.
References new_object().
◆ create()
|
static |
Create an instance based on a name If provider is empty then best available is chosen.
- Parameters
-
algo_spec algorithm name provider provider implementation to choose
- Returns
- a null pointer if the algo/provider combination cannot be found
Definition at line 73 of file kdf.cpp.
References Botan::SCAN_Name::algo_name(), Botan::SCAN_Name::arg(), Botan::SCAN_Name::arg_as_integer(), Botan::SCAN_Name::arg_count(), Botan::SCAN_Name::arg_count_between(), BOTAN_UNUSED, Botan::HashFunction::create(), Botan::MessageAuthenticationCode::create(), and Botan::fmt().
Referenced by create_or_throw(), and ~KDF().
◆ create_or_throw()
|
static |
Create an instance based on a name, or throw if the algo/provider combination cannot be found. If provider is empty then best available is chosen.
Definition at line 204 of file kdf.cpp.
References create(), and kdf().
Referenced by botan_kdf(), Botan::TLS::PSKImporter::derive_imported_psk(), Botan::ECIES_KA_Operation::derive_secret(), Botan::get_kdf(), Botan::PK_Ops::KEM_Decryption_with_KDF::KEM_Decryption_with_KDF(), Botan::PK_Ops::KEM_Encryption_with_KDF::KEM_Encryption_with_KDF(), Botan::PK_Ops::Key_Agreement_with_KDF::Key_Agreement_with_KDF(), Botan::TLS::Callbacks::tls12_protocol_specific_kdf(), and ~KDF().
◆ derive_key() [1/9]
|
inline |
Derive a key
- Parameters
-
key_len the desired output length in bytes secret the secret input secret_len size of secret in bytes salt a diversifier salt_len size of salt in bytes label purpose for the derived keying material label_len size of label in bytes
- Returns
- the derived key
Definition at line 91 of file kdf.h.
References derive_key().
Referenced by derive_key(), derive_key(), derive_key(), derive_key(), derive_key(), Botan::hkdf_expand_label(), and kdf().
◆ derive_key() [2/9]
|
inline |
Derive a key
- Parameters
-
key_len the desired output length in bytes secret the secret input secret_len size of secret in bytes salt a diversifier label purpose for the derived keying material
- Returns
- the derived key
Definition at line 179 of file kdf.h.
References derive_key().
◆ derive_key() [3/9]
|
inline |
Derive a key
- Parameters
-
key_len the desired output length in bytes secret the secret input salt a diversifier salt_len size of salt in bytes label purpose for the derived keying material
- Returns
- the derived key
Definition at line 160 of file kdf.h.
References derive_key().
◆ derive_key() [4/9]
|
inline |
Derive a key
- Parameters
-
key_len the desired output length in bytes secret the secret input salt a diversifier label purpose for the derived keying material
- Returns
- the derived key
Definition at line 140 of file kdf.h.
References perform_kdf().
◆ derive_key() [5/9]
|
inline |
Derive a key
- Parameters
-
key_len the desired output length in bytes secret the secret input salt a diversifier label purpose for the derived keying material
- Returns
- the derived key
Definition at line 110 of file kdf.h.
References derive_key().
◆ derive_key() [6/9]
|
inline |
Derive a key
- Template Parameters
-
key_len the desired output length in bytes
- Parameters
-
secret the secret input salt a diversifier label purpose for the derived keying material
- Returns
- the derived key
Definition at line 196 of file kdf.h.
◆ derive_key() [7/9]
|
inline |
◆ derive_key() [8/9]
|
inline |
Derive a key
- Template Parameters
-
key_len the desired output length in bytes
- Parameters
-
secret the secret input salt a diversifier label purpose for the derived keying material
- Returns
- the derived key
Definition at line 228 of file kdf.h.
References derive_key().
◆ derive_key() [9/9]
|
inline |
Derive a key
- Parameters
-
key the output buffer for the to-be-derived key secret the secret input salt a diversifier label purpose for the derived keying material
Definition at line 124 of file kdf.h.
References perform_kdf().
◆ kdf()
|
inline |
Derive a key
- Parameters
-
key buffer holding the derived key, must be of length key_len key_len the desired output length in bytes secret the secret input secret_len size of secret in bytes salt a diversifier salt_len size of salt in bytes label purpose for the derived keying material label_len size of label in bytes
Definition at line 67 of file kdf.h.
References derive_key(), and kdf().
Referenced by create_or_throw(), and kdf().
◆ name()
|
pure virtual |
- Returns
- KDF name
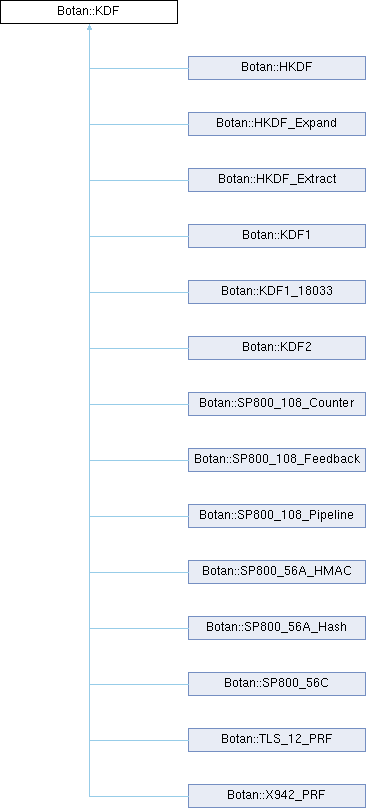
Implemented in Botan::HKDF, Botan::HKDF_Expand, Botan::HKDF_Extract, Botan::KDF1, Botan::KDF1_18033, Botan::KDF2, Botan::SP800_108_Counter, Botan::SP800_108_Feedback, Botan::SP800_108_Pipeline, Botan::SP800_56C_One_Step_Hash, Botan::SP800_56C_One_Step_HMAC, Botan::SP800_56C_One_Step_KMAC128, Botan::SP800_56C_One_Step_KMAC256, Botan::SP800_56C_Two_Step, Botan::TLS_12_PRF, and Botan::X942_PRF.
◆ new_object()
|
pure virtual |
- Returns
- new object representing the same algorithm as *this
Implemented in Botan::HKDF, Botan::HKDF_Expand, Botan::HKDF_Extract, Botan::KDF1, Botan::KDF1_18033, Botan::KDF2, Botan::SP800_108_Counter, Botan::SP800_108_Feedback, Botan::SP800_108_Pipeline, Botan::SP800_56C_One_Step_Hash, Botan::SP800_56C_One_Step_HMAC, Botan::SP800_56C_One_Step_KMAC128, Botan::SP800_56C_One_Step_KMAC256, Botan::SP800_56C_Two_Step, Botan::TLS_12_PRF, and Botan::X942_PRF.
Referenced by clone().
◆ perform_kdf()
|
protectedpure virtual |
Internal customization point for subclasses
The byte size of the key span is the number of bytes to be produced by the concrete key derivation function.
- Parameters
-
key the output buffer for the to-be-derived key secret the secret input salt a diversifier label purpose for the derived keying material
Referenced by derive_key(), and derive_key().
◆ providers()
|
static |
- Returns
- list of available providers for this algorithm, empty if not available
Definition at line 211 of file kdf.cpp.
References Botan::probe_providers_of().
Referenced by ~KDF().
The documentation for this class was generated from the following files:
Generated by