#include <tls_policy.h>
Public Member Functions | |
| virtual bool | abort_connection_on_undesired_renegotiation () const |
| virtual std::optional< std::vector< Signature_Scheme > > | acceptable_certificate_signature_schemes () const |
| virtual bool | acceptable_ciphersuite (const Ciphersuite &suite) const |
| virtual bool | acceptable_protocol_version (Protocol_Version version) const |
| virtual std::vector< Signature_Scheme > | acceptable_signature_schemes () const |
| virtual std::vector< Certificate_Type > | accepted_client_certificate_types () const |
| virtual std::vector< Certificate_Type > | accepted_server_certificate_types () const |
| virtual bool | allow_client_initiated_renegotiation () const |
| bool | allow_dtls12 () const override |
| virtual bool | allow_dtls_epoch0_restart () const |
| virtual bool | allow_insecure_renegotiation () const |
| virtual bool | allow_resumption_for_renegotiation () const |
| virtual bool | allow_server_initiated_renegotiation () const |
| virtual bool | allow_ssl_key_log_file () const |
| bool | allow_tls12 () const override |
| bool | allow_tls13 () const override |
| std::vector< std::string > | allowed_ciphers () const override |
| std::vector< std::string > | allowed_key_exchange_methods () const override |
| std::vector< std::string > | allowed_macs () const override |
| bool | allowed_signature_hash (std::string_view hash) const |
| std::vector< std::string > | allowed_signature_hashes () const override |
| bool | allowed_signature_method (std::string_view sig_method) const |
| std::vector< std::string > | allowed_signature_methods () const override |
| virtual std::vector< Signature_Scheme > | allowed_signature_schemes () const |
| virtual void | check_peer_key_acceptable (const Public_Key &public_key) const |
| virtual Group_Params | choose_key_exchange_group (const std::vector< Group_Params > &supported_by_peer, const std::vector< Group_Params > &offered_by_peer) const |
| virtual std::vector< uint16_t > | ciphersuite_list (Protocol_Version version) const |
| virtual Group_Params | default_dh_group () const |
| virtual size_t | dtls_default_mtu () const |
| virtual size_t | dtls_initial_timeout () const |
| virtual size_t | dtls_maximum_timeout () const |
| virtual bool | hash_hello_random () const |
| virtual bool | hide_unknown_users () const |
| virtual bool | include_time_in_hello_random () const |
| std::vector< Group_Params > | key_exchange_groups () const override |
| virtual std::vector< Group_Params > | key_exchange_groups_to_offer () const |
| virtual Protocol_Version | latest_supported_version (bool datagram) const |
| virtual size_t | maximum_certificate_chain_size () const |
| virtual size_t | maximum_dh_group_size () const |
| virtual size_t | maximum_handshake_message_size () const |
| virtual size_t | maximum_session_tickets_per_client_hello () const |
| virtual size_t | maximum_session_tickets_per_connection () const |
| virtual size_t | minimum_dh_group_size () const |
| virtual size_t | minimum_ecdh_group_size () const |
| virtual size_t | minimum_ecdsa_group_size () const |
| virtual uint64_t | minimum_key_update_interval_ms () const |
| virtual size_t | minimum_rsa_bits () const |
| size_t | minimum_signature_strength () const override |
| virtual bool | negotiate_encrypt_then_mac () const |
| virtual size_t | new_session_tickets_upon_handshake_success () const |
| virtual bool | only_resume_with_exact_version () const |
| virtual void | print (std::ostream &o) const |
| virtual std::optional< uint16_t > | record_size_limit () const |
| virtual bool | request_client_certificate_authentication () const |
| virtual bool | require_cert_revocation_info () const |
| virtual bool | require_client_certificate_authentication () const |
| virtual bool | require_extended_master_secret () const |
| virtual bool | reuse_session_tickets () const |
| virtual bool | server_uses_own_ciphersuite_preferences () const |
| virtual std::chrono::seconds | session_ticket_lifetime () const |
| virtual std::vector< uint16_t > | srtp_profiles () const |
| virtual bool | support_cert_status_message () const |
| virtual bool | tls_13_middlebox_compatibility_mode () const |
| std::string | to_string () const |
| virtual bool | use_ecc_point_compression () const |
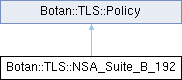
Detailed Description
NSA Suite B 192-bit security level (RFC 6460)
Definition at line 655 of file tls_policy.h.
Member Function Documentation
◆ abort_connection_on_undesired_renegotiation()
|
virtualinherited |
If true, a request to renegotiate will close the connection with a fatal alert. Otherwise, a warning alert is sent.
Default: false
- Note
- Has no effect for TLS 1.3 connections.
Definition at line 454 of file tls_policy.cpp.
◆ acceptable_certificate_signature_schemes()
|
virtualinherited |
Return a list of schemes we are willing to accept for signatures in certificates.
By default, the same restrictions as in acceptable_signature_schemes() apply.
- Returns
- std::nullopt if the same restrictions as defined in acceptable_signature_schemes() should apply
Definition at line 48 of file tls_policy.cpp.
Referenced by Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_12::Client_Hello_12(), and Botan::TLS::Client_Hello_13::Client_Hello_13().
◆ acceptable_ciphersuite()
|
virtualinherited |
Allows policy to reject any ciphersuites which are undesirable for whatever reason without having to reimplement ciphersuite_list
Definition at line 361 of file tls_policy.cpp.
References allowed_ciphers(), allowed_macs(), Botan::TLS::Ciphersuite::cipher_algo(), Botan::TLS::Ciphersuite::mac_algo(), and Botan::value_exists().
Referenced by ciphersuite_list().
◆ acceptable_protocol_version()
|
virtualinherited |
- Returns
- true if and only if we are willing to accept this version Default accepts TLS v1.2 and later or DTLS v1.2 or later.
Definition at line 323 of file tls_policy.cpp.
References allow_dtls12(), allow_tls12(), allow_tls13(), and BOTAN_UNUSED.
Referenced by Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_13::highest_supported_version(), and latest_supported_version().
◆ acceptable_signature_schemes()
|
virtualinherited |
Return a list of schemes we are willing to accept
Definition at line 44 of file tls_policy.cpp.
References allowed_signature_schemes().
Referenced by Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_12::Client_Hello_12(), and Botan::TLS::Client_Hello_13::Client_Hello_13().
◆ accepted_client_certificate_types()
|
virtualinherited |
Returns a list of accepted certificate types for client authentication in order of preference. See RFC 7250 and RFC 8446 4.4.2 for details. Defaults to X509 only.
Note that it is the application's responsibility to provide public keys and/or certificates according to the specification in this list via the Credentials_Manager.
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 458 of file tls_policy.cpp.
References Botan::TLS::X509.
Referenced by Botan::TLS::Text_Policy::accepted_client_certificate_types(), Botan::TLS::Client_Hello_13::Client_Hello_13(), and print().
◆ accepted_server_certificate_types()
|
virtualinherited |
Returns a list of accepted certificate types for server authentication in order of preference. See RFC 7250 and RFC 8446 4.4.2 for details. Defaults to X509 only.
Note that it is the application's responsibility to provide public keys and/or certificates according to the specification in this list via the Credentials_Manager.
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 462 of file tls_policy.cpp.
References Botan::TLS::X509.
Referenced by Botan::TLS::Text_Policy::accepted_server_certificate_types(), Botan::TLS::Client_Hello_13::Client_Hello_13(), and print().
◆ allow_client_initiated_renegotiation()
|
virtualinherited |
Consulted by server side. If true, allows clients to initiate a new handshake
If this function returns true, a server will accept a client-initiated renegotiation attempt. Otherwise it will send the client a non-fatal TLS::AlertType::NoRenegotiation alert.
Default: false
- Note
- Has no effect for TLS 1.3 connections.
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 366 of file tls_policy.cpp.
Referenced by Botan::TLS::Text_Policy::allow_client_initiated_renegotiation().
◆ allow_dtls12()
|
inlineoverridevirtual |
Allow DTLS v1.2
Reimplemented from Botan::TLS::Policy.
Definition at line 681 of file tls_policy.h.
◆ allow_dtls_epoch0_restart()
|
virtualinherited |
If true, then allow a DTLS client to restart a connection to the same server association as described in section 4.2.8 of the DTLS RFC
Definition at line 466 of file tls_policy.cpp.
Referenced by Botan::TLS::Channel_Impl_12::from_peer().
◆ allow_insecure_renegotiation()
|
virtualinherited |
Allow renegotiation even if the counterparty doesn't support the secure renegotiation extension.
Default: false
- Warning
- Changing this to true exposes you to injected plaintext attacks. Read RFC 5746 for background.
- Note
- Has no effect for TLS 1.3 connections.
Reimplemented in Botan::TLS::BSI_TR_02102_2, and Botan::TLS::Text_Policy.
Definition at line 374 of file tls_policy.cpp.
Referenced by Botan::TLS::Text_Policy::allow_insecure_renegotiation(), and print().
◆ allow_resumption_for_renegotiation()
|
virtualinherited |
- Note
- Has no effect for TLS 1.3 connections.
Definition at line 430 of file tls_policy.cpp.
Referenced by Botan::TLS::Channel_Impl_12::renegotiate().
◆ allow_server_initiated_renegotiation()
|
virtualinherited |
Consulted by client side. If true, allows servers to initiate a new handshake
If this function returns true, a client will accept a server-initiated renegotiation attempt. Otherwise it will send the server a non-fatal TLS::AlertType::NoRenegotiation alert.
Default: false
- Note
- Has no effect for TLS 1.3 connections.
Reimplemented in Botan::TLS::BSI_TR_02102_2, and Botan::TLS::Text_Policy.
Definition at line 370 of file tls_policy.cpp.
Referenced by Botan::TLS::Text_Policy::allow_server_initiated_renegotiation(), and print().
◆ allow_ssl_key_log_file()
|
virtualinherited |
Allow ssl key log file
- Note
- If function returns true, then Callbacks::tls_ssl_key_log_data will be invoked containing secret information for logging purposes
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 25 of file tls_policy.cpp.
Referenced by Botan::TLS::Text_Policy::allow_ssl_key_log_file(), and print().
◆ allow_tls12()
|
inlineoverridevirtual |
Allow TLS v1.2
Reimplemented from Botan::TLS::Policy.
Definition at line 677 of file tls_policy.h.
◆ allow_tls13()
|
inlineoverridevirtual |
Allow TLS v1.3
Reimplemented from Botan::TLS::Policy.
Definition at line 679 of file tls_policy.h.
◆ allowed_ciphers()
|
inlineoverridevirtual |
Returns a list of ciphers we are willing to negotiate, in order of preference.
Reimplemented from Botan::TLS::Policy.
Definition at line 657 of file tls_policy.h.
◆ allowed_key_exchange_methods()
|
inlineoverridevirtual |
Returns a list of key exchange algorithms we are willing to use, in order of preference. Allowed values: DH, empty string (representing RSA using server certificate key)
Reimplemented from Botan::TLS::Policy.
Definition at line 665 of file tls_policy.h.
◆ allowed_macs()
|
inlineoverridevirtual |
Returns a list of MAC algorithms we are willing to use.
Reimplemented from Botan::TLS::Policy.
Definition at line 663 of file tls_policy.h.
◆ allowed_signature_hash()
|
inherited |
Definition at line 116 of file tls_policy.cpp.
References allowed_signature_hashes(), and Botan::value_exists().
Referenced by allowed_signature_schemes(), and Botan::TLS::Handshake_State::choose_sig_format().
◆ allowed_signature_hashes()
|
inlineoverridevirtual |
Returns a list of hash algorithms we are willing to use for signatures, in order of preference.
Reimplemented from Botan::TLS::Policy.
Definition at line 659 of file tls_policy.h.
◆ allowed_signature_method()
|
inherited |
Definition at line 112 of file tls_policy.cpp.
References allowed_signature_methods(), and Botan::value_exists().
Referenced by allowed_signature_schemes(), Botan::TLS::Certificate_13::Certificate_13(), and Botan::TLS::Handshake_State::parse_sig_format().
◆ allowed_signature_methods()
|
inlineoverridevirtual |
Returns a list of signature algorithms we are willing to use, in order of preference.
Reimplemented from Botan::TLS::Policy.
Definition at line 669 of file tls_policy.h.
◆ allowed_signature_schemes()
|
virtualinherited |
Definition at line 29 of file tls_policy.cpp.
References Botan::TLS::Signature_Scheme::all_available_schemes(), allowed_signature_hash(), and allowed_signature_method().
Referenced by acceptable_signature_schemes(), Botan::TLS::Certificate_Verify_13::Certificate_Verify_13(), and Botan::TLS::Handshake_State::choose_sig_format().
◆ check_peer_key_acceptable()
|
virtualinherited |
Allows the policy to examine peer public keys. Throw an exception if the key should be rejected. Default implementation checks against policy values minimum_dh_group_size(), minimum_rsa_bits(), minimum_ecdsa_group_size(), and minimum_ecdh_group_size().
Override if you'd like to perform some other kind of test on (or logging of) the peer's keys.
Definition at line 281 of file tls_policy.cpp.
References Botan::Asymmetric_Key::algo_name(), Botan::Public_Key::key_length(), minimum_dh_group_size(), minimum_ecdh_group_size(), minimum_ecdsa_group_size(), and minimum_rsa_bits().
Referenced by Botan::TLS::Certificate_13::Certificate_13(), Botan::TLS::Callbacks::tls_ephemeral_key_agreement(), Botan::TLS::Callbacks::tls_kem_encapsulate(), Botan::TLS::Certificate_Verify_12::verify(), and Botan::TLS::Server_Key_Exchange::verify().
◆ choose_key_exchange_group()
|
virtualinherited |
Select a key exchange group to use, from the list of groups sent by the peer. In TLS 1.3 handshakes the peer might have provided cryptographic material for a subset of its available groups. Choosing a group for which no share was provided will result in an additional round trip. If none are acceptable, return Group_Params::NONE.
By default this will try to optimize for less round trips even if this results in the usage of a less preferred group.
Definition at line 124 of file tls_policy.cpp.
References key_exchange_groups(), and Botan::value_exists().
Referenced by Botan::TLS::Client_Key_Exchange::Client_Key_Exchange(), Botan::TLS::Server_Hello_13::create(), and Botan::TLS::Server_Key_Exchange::Server_Key_Exchange().
◆ ciphersuite_list()
|
virtualinherited |
Return allowed ciphersuites, in order of preference for the provided protocol version.
- Parameters
-
version the exact protocol version to select supported and allowed ciphersuites for
Definition at line 577 of file tls_policy.cpp.
References acceptable_ciphersuite(), Botan::TLS::Ciphersuite::all_known_ciphersuites(), allowed_ciphers(), allowed_key_exchange_methods(), allowed_macs(), allowed_signature_methods(), Botan::TLS::IMPLICIT, Botan::TLS::Protocol_Version::is_pre_tls_13(), and Botan::value_exists().
Referenced by Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_12::Client_Hello_12(), and Botan::TLS::Client_Hello_13::Client_Hello_13().
◆ default_dh_group()
|
virtualinherited |
For ephemeral Diffie-Hellman key exchange, the server sends a group parameter. Return the 2 Byte TLS group identifier specifying the group parameter a server should use.
Default: 2048 bit IETF IPsec group ("modp/ietf/2048")
- Note
- Has no effect for TLS 1.3 connections.
Definition at line 165 of file tls_policy.cpp.
References key_exchange_groups().
Referenced by Botan::TLS::Server_Key_Exchange::Server_Key_Exchange().
◆ dtls_default_mtu()
|
virtualinherited |
- Returns
- the default MTU for DTLS
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 495 of file tls_policy.cpp.
Referenced by Botan::TLS::Channel_Impl_12::create_handshake_state(), and Botan::TLS::Text_Policy::dtls_default_mtu().
◆ dtls_initial_timeout()
|
virtualinherited |
- Returns
- the initial timeout for DTLS
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 487 of file tls_policy.cpp.
Referenced by Botan::TLS::Channel_Impl_12::create_handshake_state(), and Botan::TLS::Text_Policy::dtls_initial_timeout().
◆ dtls_maximum_timeout()
|
virtualinherited |
- Returns
- the maximum timeout for DTLS
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 491 of file tls_policy.cpp.
Referenced by Botan::TLS::Channel_Impl_12::create_handshake_state(), and Botan::TLS::Text_Policy::dtls_maximum_timeout().
◆ hash_hello_random()
|
virtualinherited |
Hash the RNG output for the client/server hello random. This is a pre-caution to avoid writing "raw" RNG output to the wire.
There's not normally a reason to disable this, except when deterministic output is required for testing.
Default: true
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 438 of file tls_policy.cpp.
Referenced by Botan::TLS::Text_Policy::hash_hello_random(), Botan::TLS::make_hello_random(), and print().
◆ hide_unknown_users()
|
virtualinherited |
The PSK suites work using an identifier along with a shared secret. If this function returns true, when an identifier that the server does not recognize is provided by a client, a random shared secret will be generated in such a way that a client should not be able to tell the difference between the identifier not being known and the secret being wrong. This can help protect against some username probing attacks. If it returns false, the server will instead send an TLS::AlertType::UnknownPSKIdentity alert when an unknown identifier is used.
Default: false
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 406 of file tls_policy.cpp.
Referenced by Botan::TLS::Client_Key_Exchange::Client_Key_Exchange(), Botan::TLS::Text_Policy::hide_unknown_users(), and print().
◆ include_time_in_hello_random()
|
virtualinherited |
The protocol dictates that the first 32 bits of the random field are the current time in seconds. However this allows client fingerprinting attacks. Set to false to disable, in which case random bytes will be used instead.
Default: true
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 402 of file tls_policy.cpp.
Referenced by Botan::TLS::Text_Policy::include_time_in_hello_random(), Botan::TLS::make_hello_random(), and print().
◆ key_exchange_groups()
|
inlineoverridevirtual |
Return a list of ECC curve and DH group TLS identifiers we are willing to use, in order of preference. The default ordering puts the best performing ECC first.
Default: Group_Params::X25519, Group_Params::SECP256R1, Group_Params::BRAINPOOL256R1, Group_Params::SECP384R1, Group_Params::BRAINPOOL384R1, Group_Params::SECP521R1, Group_Params::BRAINPOOL512R1, Group_Params::FFDHE_2048, Group_Params::FFDHE_3072, Group_Params::FFDHE_4096, Group_Params::FFDHE_6144, Group_Params::FFDHE_8192
No other values are currently defined.
Reimplemented from Botan::TLS::Policy.
Definition at line 673 of file tls_policy.h.
◆ key_exchange_groups_to_offer()
|
virtualinherited |
Return a list of groups to provide prepared key share offers in the initial client hello for. Groups in this list must be reflected in key_exchange_groups() and in the same order. If an empty list is returned, no prepared key share offers are sent and the decision of the group to use is left to the server.
Default: the most preferred group from key_exchange_groups().
- Note
- Has an effect on TLS 1.3 clients, only.
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 215 of file tls_policy.cpp.
References BOTAN_ASSERT, and key_exchange_groups().
Referenced by Botan::TLS::Text_Policy::key_exchange_groups_to_offer(), and print().
◆ latest_supported_version()
|
virtualinherited |
Returns the most recent protocol version we are willing to use, for either TLS or DTLS depending on datagram param. Shouldn't ever need to override this unless you want to allow a user to disable specific TLS versions.
Definition at line 344 of file tls_policy.cpp.
References acceptable_protocol_version().
◆ maximum_certificate_chain_size()
|
virtualinherited |
- Returns
- the maximum size of the certificate chain, in bytes. Return 0 to disable this and accept any size.
Definition at line 474 of file tls_policy.cpp.
Referenced by Botan::TLS::Certificate_12::Certificate_12(), and Botan::TLS::Certificate_13::Certificate_13().
◆ maximum_dh_group_size()
|
virtualinherited |
Largest DH group size (in bits) the client will accept from a server.
Default: 8192 bits (the largest FFDHE group)
This only affects the TLS 1.2 client
Definition at line 248 of file tls_policy.cpp.
Referenced by Botan::TLS::Client_Key_Exchange::Client_Key_Exchange().
◆ maximum_handshake_message_size()
|
virtualinherited |
- Returns
- the maximum size of a single handshake message, in bytes. Messages larger than this will be rejected prior to processing. Return 0 to disable this and accept any size.
Definition at line 470 of file tls_policy.cpp.
◆ maximum_session_tickets_per_client_hello()
|
virtualinherited |
Defines the maximum number of session tickets a client might offer in a single resumption attempt. Must be greater than 0.
TODO: Currently, the TLS 1.3 client implementation supports exactly one ticket per handshake. RFC 8446 allows for an arbitrary amount, though.
Default: 1
- Note
- Has an effect on TLS 1.3 connections, only.
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 307 of file tls_policy.cpp.
Referenced by Botan::TLS::Session_Manager::find(), Botan::TLS::Text_Policy::maximum_session_tickets_per_client_hello(), and print().
◆ maximum_session_tickets_per_connection()
|
virtualinherited |
- Returns
- the maximum number of NewSessionTicket messages to accept from a server on a single connection. Return 0 to disable the limit.
- Note
- Only applies to TLS 1.3 client connections.
Definition at line 482 of file tls_policy.cpp.
◆ minimum_dh_group_size()
|
virtualinherited |
Return the minimum DH group size we're willing to use
Return the minimum size in bits for a Diffie-Hellman group that a client will accept. Due to the design of the protocol the client has only two options - accept the group, or reject it with a fatal alert then attempt to reconnect after disabling ephemeral Diffie-Hellman.
Default: 2048 bits
This only affects the TLS 1.2 client
Reimplemented in Botan::TLS::BSI_TR_02102_2, and Botan::TLS::Text_Policy.
Definition at line 244 of file tls_policy.cpp.
Referenced by check_peer_key_acceptable(), Botan::TLS::Client_Key_Exchange::Client_Key_Exchange(), Botan::TLS::Text_Policy::minimum_dh_group_size(), and print().
◆ minimum_ecdh_group_size()
|
virtualinherited |
Return the minimum ECDH group size we're willing to use for key exchange
Default 255, allowing x25519 and larger x25519 is the smallest curve we will negotiate P-521 is the largest
Reimplemented in Botan::TLS::BSI_TR_02102_2, and Botan::TLS::Text_Policy.
Definition at line 257 of file tls_policy.cpp.
Referenced by check_peer_key_acceptable(), Botan::TLS::Text_Policy::minimum_ecdh_group_size(), and print().
◆ minimum_ecdsa_group_size()
|
virtualinherited |
For ECDSA authenticated ciphersuites, the smallest key size the client will accept. This policy is currently only enforced on the server by the client.
Default: 256
Reimplemented in Botan::TLS::BSI_TR_02102_2, and Botan::TLS::Text_Policy.
Definition at line 252 of file tls_policy.cpp.
Referenced by check_peer_key_acceptable(), and Botan::TLS::Text_Policy::minimum_ecdsa_group_size().
◆ minimum_key_update_interval_ms()
|
virtualinherited |
- Returns
- the minimum number of milliseconds that must elapse between two received KeyUpdate messages. If a KeyUpdate arrives sooner than this interval after the previous one, the connection is terminated. Return 0 to disable rate limiting.
- Note
- Only applies to TLS 1.3 connections.
Definition at line 478 of file tls_policy.cpp.
◆ minimum_rsa_bits()
|
virtualinherited |
Return the minimum bit size we're willing to accept for RSA key exchange or server signatures.
It does not place any requirements on the size of any RSA signature(s) which were used to check the server certificate. This is only concerned with the server's public key.
Default is 2048 which is smallest RSA key size still secure for medium term security.
Reimplemented in Botan::TLS::BSI_TR_02102_2, and Botan::TLS::Text_Policy.
Definition at line 270 of file tls_policy.cpp.
Referenced by check_peer_key_acceptable(), Botan::TLS::Text_Policy::minimum_rsa_bits(), and print().
◆ minimum_signature_strength()
|
inlineoverridevirtual |
The minimum signature strength we will accept
Returning 80 allows RSA 1024 and SHA-1. Values larger than 80 disable SHA-1 support. Returning 110 allows RSA 2048. Return 128 to force ECC (P-256) or large (~3000 bit) RSA keys.
Default is 110
Reimplemented from Botan::TLS::Policy.
Definition at line 675 of file tls_policy.h.
◆ negotiate_encrypt_then_mac()
|
virtualinherited |
Indicates whether the encrypt-then-MAC extension should be negotiated (RFC 7366)
- Note
- Has no effect for TLS 1.3 connections.
Reimplemented in Botan::TLS::BSI_TR_02102_2, and Botan::TLS::Text_Policy.
Definition at line 414 of file tls_policy.cpp.
Referenced by Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_13::Client_Hello_13(), Botan::TLS::Text_Policy::negotiate_encrypt_then_mac(), print(), Botan::TLS::Server_Hello_12::Server_Hello_12(), and Botan::TLS::Server_Hello_12::Server_Hello_12().
◆ new_session_tickets_upon_handshake_success()
|
virtualinherited |
Return the number of new session tickets a TLS 1.3 server should issue automatically upon a successful handshake. Note that applications can use TLS::Server::send_new_session_tickets() regardless of this policy.
For convenience (and compatibility with the TLS 1.2 behaviour), this returns '1' by default.
- Note
- Has an effect on TLS 1.3 connections, only.
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 319 of file tls_policy.cpp.
Referenced by Botan::TLS::Text_Policy::new_session_tickets_upon_handshake_success(), and print().
◆ only_resume_with_exact_version()
|
virtualinherited |
Only resume sessions when their original protocol version matches the current version exactly.
Default: true
Definition at line 442 of file tls_policy.cpp.
◆ print()
|
virtualinherited |
Convert this policy to a printable format.
- Parameters
-
o stream to be printed to
Definition at line 693 of file tls_policy.cpp.
References accepted_client_certificate_types(), accepted_server_certificate_types(), allow_dtls12(), allow_insecure_renegotiation(), allow_server_initiated_renegotiation(), allow_ssl_key_log_file(), allow_tls12(), allow_tls13(), allowed_ciphers(), allowed_key_exchange_methods(), allowed_macs(), allowed_signature_hashes(), allowed_signature_methods(), hash_hello_random(), hide_unknown_users(), include_time_in_hello_random(), key_exchange_groups(), key_exchange_groups_to_offer(), maximum_session_tickets_per_client_hello(), minimum_dh_group_size(), minimum_ecdh_group_size(), minimum_rsa_bits(), minimum_signature_strength(), negotiate_encrypt_then_mac(), new_session_tickets_upon_handshake_success(), record_size_limit(), require_extended_master_secret(), reuse_session_tickets(), server_uses_own_ciphersuite_preferences(), session_ticket_lifetime(), support_cert_status_message(), and tls_13_middlebox_compatibility_mode().
Referenced by to_string().
◆ record_size_limit()
|
virtualinherited |
Defines the maximum TLS record length for TLS connections. This is based on the Record Size Limit extension described in RFC 8449. By default (i.e. if std::nullopt is returned), TLS clients will omit this extension altogether.
This value may be between 64 and 16385 (TLS 1.3) or 16384 (TLS 1.2).
- Note
- This is currently not implemented for TLS 1.2, hence the limit won't be negotiated by TLS 1.3 clients that support downgrading to TLS 1.2 (i.e. allow_tls12() returning true).
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 422 of file tls_policy.cpp.
Referenced by Botan::TLS::Client_Hello_13::Client_Hello_13(), Botan::TLS::Encrypted_Extensions::Encrypted_Extensions(), and print().
◆ request_client_certificate_authentication()
|
virtualinherited |
Indicate if client certificate authentication is requested. If true, then a cert will be requested.
Definition at line 450 of file tls_policy.cpp.
References require_client_certificate_authentication().
Referenced by Botan::TLS::Certificate_Request_13::maybe_create().
◆ require_cert_revocation_info()
|
virtualinherited |
Return if certificate revocation info (CRL/OCSP) is required
If true, certificates won't be trusted unless a valid CRL or OCSP response was examined.
Default: true
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 266 of file tls_policy.cpp.
Referenced by Botan::TLS::Text_Policy::require_cert_revocation_info(), and Botan::TLS::Callbacks::tls_verify_cert_chain().
◆ require_client_certificate_authentication()
|
virtualinherited |
Indicate if client certificate authentication is required. If true, then a cert will be requested and if the client does not send a certificate the connection will be closed.
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 446 of file tls_policy.cpp.
Referenced by request_client_certificate_authentication(), and Botan::TLS::Text_Policy::require_client_certificate_authentication().
◆ require_extended_master_secret()
|
virtualinherited |
Require that TLS 1.2 / DTLS 1.2 handshakes use the Extended Master Secret extension (RFC 7627). When true, both the server and the client abort fresh handshakes whose peer did not negotiate EMS. RFC 9325 4.4 recommends requiring this extension.
- Note
- Has no effect for TLS 1.3 connections, where the equivalent binding is built in.
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 418 of file tls_policy.cpp.
Referenced by print(), and Botan::TLS::Text_Policy::require_extended_master_secret().
◆ reuse_session_tickets()
|
virtualinherited |
Decides whether stored session tickets should be used multiple times (until their lifetime runs out). This might allow passive observers to correlate connections (RFC 8446 Appendix C.4). This has no effect on TLS 1.2 resumptions based on session IDs as those are negotiated in the clear anyway.
Default: false
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 315 of file tls_policy.cpp.
Referenced by Botan::TLS::Session_Manager::find(), print(), and Botan::TLS::Text_Policy::reuse_session_tickets().
◆ server_uses_own_ciphersuite_preferences()
|
virtualinherited |
Default: true
- Returns
- true if servers should choose the ciphersuite matching their highest preference, rather than the clients. Has no effect on client side.
Reimplemented in Botan::TLS::BSI_TR_02102_2, and Botan::TLS::Text_Policy.
Definition at line 410 of file tls_policy.cpp.
Referenced by print(), and Botan::TLS::Text_Policy::server_uses_own_ciphersuite_preferences().
◆ session_ticket_lifetime()
|
virtualinherited |
Return the allowed lifetime of a session ticket. If 0, session tickets do not expire until the session ticket key rolls over. For TLS 1.3 session tickets the lifetime must not be longer than seven days. Expired session tickets cannot be used to resume a session.
Default: 1 day
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 311 of file tls_policy.cpp.
Referenced by print(), Botan::TLS::Session_Manager::retrieve(), and Botan::TLS::Text_Policy::session_ticket_lifetime().
◆ srtp_profiles()
|
virtualinherited |
If this returns a non-empty vector, and DTLS is negotiated, then we will also attempt to negotiate the SRTP extension from RFC 5764 using the returned values as the profile ids.
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 500 of file tls_policy.cpp.
Referenced by Botan::TLS::Client_Hello_12::Client_Hello_12().
◆ support_cert_status_message()
|
virtualinherited |
Indicates whether certificate status messages should be supported
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 426 of file tls_policy.cpp.
Referenced by Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_12::Client_Hello_12(), Botan::TLS::Client_Hello_13::Client_Hello_13(), print(), Botan::TLS::Server_Hello_12::Server_Hello_12(), and Botan::TLS::Text_Policy::support_cert_status_message().
◆ tls_13_middlebox_compatibility_mode()
|
virtualinherited |
Defines whether or not the middlebox compatibility mode should be used. Enabled by default.
RFC 8446 Appendix D.4 [This makes] the TLS 1.3 handshake resemble TLS 1.2 session resumption, which improves the chance of successfully connecting through middleboxes.
Default: true
- Note
- Has an effect on TLS 1.3 connections, only.
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 434 of file tls_policy.cpp.
Referenced by Botan::TLS::Client_Hello_13::Client_Hello_13(), print(), and Botan::TLS::Text_Policy::tls_13_middlebox_compatibility_mode().
◆ to_string()
|
inherited |
Convert this policy to a printable format. Same as calling print on a ostringstream and reading o.str()
Definition at line 735 of file tls_policy.cpp.
References print().
◆ use_ecc_point_compression()
|
virtualinherited |
Request that ECC curve points are sent compressed
Signals that we prefer ECC points to be compressed when transmitted to us. The other party may not support ECC point compression and therefore may still send points uncompressed.
Note that the certificate used during authentication must also follow the other party's preference.
- Note
- Support for EC point compression is deprecated and will be removed in a future major release. TLS 1.3 does not support point compression at all (see RFC 8446 4.2.8.2)
Reimplemented in Botan::TLS::Text_Policy.
Definition at line 120 of file tls_policy.cpp.
Referenced by Botan::TLS::Client_Hello_13::Client_Hello_13(), and Botan::TLS::Text_Policy::use_ecc_point_compression().
The documentation for this class was generated from the following file:
- src/lib/tls/tls_policy.h
Generated by