#include <pubkey.h>
Public Member Functions | |
| secure_vector< uint8_t > | decrypt (const uint8_t in[], size_t length) const |
| secure_vector< uint8_t > | decrypt (std::span< const uint8_t > in) const |
| secure_vector< uint8_t > | decrypt_or_random (const uint8_t in[], size_t length, size_t expected_pt_len, RandomNumberGenerator &rng) const |
| secure_vector< uint8_t > | decrypt_or_random (const uint8_t in[], size_t length, size_t expected_pt_len, RandomNumberGenerator &rng, const uint8_t required_content_bytes[], const uint8_t required_content_offsets[], size_t required_contents) const |
| PK_Decryptor & | operator= (const PK_Decryptor &)=delete |
| PK_Decryptor & | operator= (PK_Decryptor &&) noexcept=default |
| PK_Decryptor ()=default | |
| PK_Decryptor (const PK_Decryptor &)=delete | |
| PK_Decryptor (PK_Decryptor &&) noexcept=default | |
| virtual size_t | plaintext_length (size_t ctext_len) const =0 |
| virtual | ~PK_Decryptor ()=default |
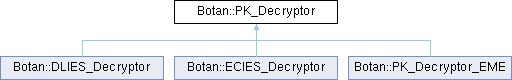
Detailed Description
Constructor & Destructor Documentation
◆ PK_Decryptor() [1/3]
|
default |
Referenced by operator=(), operator=(), PK_Decryptor(), and PK_Decryptor().
◆ ~PK_Decryptor()
|
virtualdefault |
◆ PK_Decryptor() [2/3]
|
delete |
References PK_Decryptor().
◆ PK_Decryptor() [3/3]
|
defaultnoexcept |
References PK_Decryptor().
Member Function Documentation
◆ decrypt() [1/2]
| secure_vector< uint8_t > Botan::PK_Decryptor::decrypt | ( | const uint8_t | in[], |
| size_t | length ) const |
Decrypt a ciphertext, throwing an exception if the input seems to be invalid (eg due to an accidental or malicious error in the ciphertext).
- Parameters
-
in the ciphertext as a byte array length the length of the above byte array
- Returns
- decrypted message
Definition at line 21 of file pubkey.cpp.
Referenced by Botan::KeyPair::encryption_consistency_check().
◆ decrypt() [2/2]
|
inline |
Same as above, but taking a vector
- Parameters
-
in the ciphertext
- Returns
- decrypted message
Definition at line 95 of file pubkey.h.
References decrypt().
Referenced by decrypt().
◆ decrypt_or_random() [1/2]
| secure_vector< uint8_t > Botan::PK_Decryptor::decrypt_or_random | ( | const uint8_t | in[], |
| size_t | length, | ||
| size_t | expected_pt_len, | ||
| RandomNumberGenerator & | rng ) const |
Decrypt a ciphertext. If the ciphertext is invalid (eg due to invalid padding) or is not the expected length, instead returns a random string of the expected length. Use to avoid oracle attacks, especially against PKCS #1 v1.5 decryption.
Definition at line 85 of file pubkey.cpp.
References decrypt_or_random().
Referenced by Botan::TLS::Client_Key_Exchange::Client_Key_Exchange(), and decrypt_or_random().
◆ decrypt_or_random() [2/2]
| secure_vector< uint8_t > Botan::PK_Decryptor::decrypt_or_random | ( | const uint8_t | in[], |
| size_t | length, | ||
| size_t | expected_pt_len, | ||
| RandomNumberGenerator & | rng, | ||
| const uint8_t | required_content_bytes[], | ||
| const uint8_t | required_content_offsets[], | ||
| size_t | required_contents ) const |
Decrypt a ciphertext. If the ciphertext is invalid (eg due to invalid padding) or is not the expected length, instead returns a random string of the expected length. Use to avoid oracle attacks, especially against PKCS #1 v1.5 decryption.
Additionally checks (also in const time) that: contents[required_content_offsets[i]] == required_content_bytes[i] for 0 <= i < required_contents
Used for example in TLS, which encodes the client version in the content bytes: if there is any timing variation the version check can be used as an oracle to recover the key.
Definition at line 33 of file pubkey.cpp.
References BOTAN_ASSERT, Botan::CT::Mask< T >::is_equal(), and Botan::RandomNumberGenerator::random_vec().
◆ operator=() [1/2]
|
delete |
References PK_Decryptor().
◆ operator=() [2/2]
|
defaultnoexcept |
References PK_Decryptor().
◆ plaintext_length()
|
pure virtual |
Return an upper bound on the plaintext length for a particular ciphertext input length
Implemented in Botan::PK_Decryptor_EME.
The documentation for this class was generated from the following files:
- src/lib/pubkey/pubkey.h
- src/lib/pubkey/pubkey.cpp
Generated by